最新要闻
- 实时焦点:不是我说 iPhone拍照怎么就像富士相机了?
- 世界热推荐:NVIDIA黄仁勋:我们从未忘记游戏玩家!
- 号称使用AI独立管理基金的私募改口了:AI并非主要用于交易 热点
- 人间第一情歌词完整版原唱_人间第一情歌词|全球看热讯
- 实时焦点:今金贷最新退付消息:2023年兑付最新声明退付通知(退付进展告知)
- 曝华为版ChatGPT将下月发布 名为“盘古Chat”-当前独家
- 每日热议!128秒回顾中国载人航天高燃时刻:杨利伟 居功至伟!
- 【环球报资讯】假鸡翅怎么做法?
- 撼迅AMD显卡抹错硅脂 温度高达110℃!曝生产线自证清白
- MPV无敌手 比亚迪赵长江:腾势D9月销将达1.5万-每日看点
- 专访:美国没有资格充当民主人权教师爷——访俄政治学家米尔扎扬-世界热消息
- 可提速400公里!成渝中线高铁两大隧道同时进洞
- 天涯老用户自救 结果一地鸡毛:情怀 是最不值钱的东西
- 24点结束 腾讯视频VIP年卡+京东PLUS年卡138元 环球热门
- 十字军东征——现代社会可能重演吗?
- 京东手机金榜出炉:Redmi K60力压iPhone 14夺冠
手机

iphone11大小尺寸是多少?苹果iPhone11和iPhone13的区别是什么?
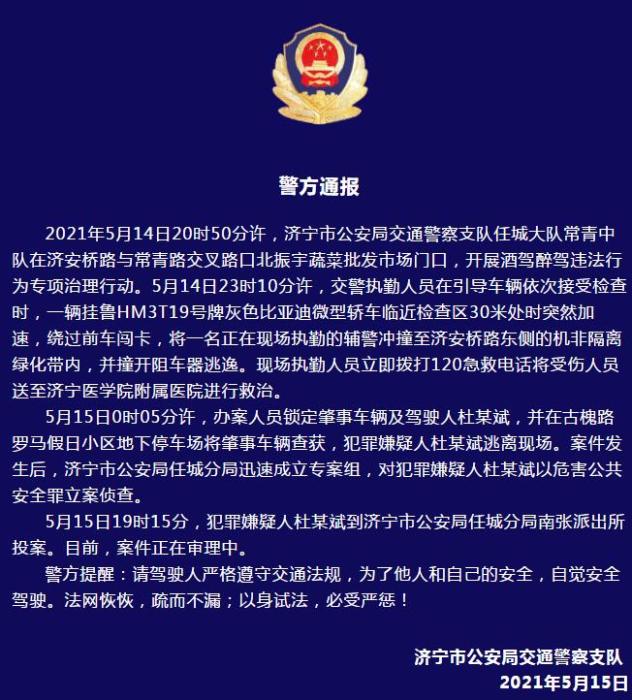
警方通报辅警执法直播中被撞飞:犯罪嫌疑人已投案
- iphone11大小尺寸是多少?苹果iPhone11和iPhone13的区别是什么?
- 警方通报辅警执法直播中被撞飞:犯罪嫌疑人已投案
- 男子被关545天申国赔:获赔18万多 驳回精神抚慰金
- 3天内26名本土感染者,辽宁确诊人数已超安徽
- 广西柳州一男子因纠纷杀害三人后自首
- 洱海坠机4名机组人员被批准为烈士 数千干部群众悼念
家电
【DNS】域名服务 Bind实现
一、域名解析过程
DNS域名完整解析过程
1、查询本地 hosts文件 解析记录
(相关资料图)
2、查询客户端本地DNS缓存记录
3、访问DNS转发(缓存)服务器本地缓存记录
4、转发到权威服务器查询本地缓存记录
5、访问权威服务器解析记录
6、权威服务器迭代查询
6.1、访问子域权威服务器查询本地缓存记录
6.2、访问子域解析记录
7、访问根服务器解析记录
8、访问一级域名服务器解析记录
.......
二、DNS解析记录类型
1、DNS服务器类型
主DNS服务器
管理和维护所负责解析的域内解析库的服务器
从DNS服务器
从主服务器或从服务器复制(区域传输)解析库副本
缓存DNS服务器(转发器)
将客户端请求转发到指定的DNS服务器上,并将指定DNS服务器返回结果缓存到本地DNS缓存记录中,缓存DNS服务器自身不保存解析库数据,不使用自身进行域名解析。
2、解析结果类型
- 肯定答案:存在对应的查询结果
- 否定答案:请求的条目不存在等原因导致无法返回结果
- 权威答案:直接由存在此查询结果的DNS服务器(权威服务器)返回的结果
- 非权威答案:有其他非权威服务器返回的查询结果
3、资源记录RR(Resource Record)
区域解析库
有众多资源记录RR(Resource Record)组成
记录类型:SOA、A、AAAA、NS、CNAME、MX、TXT、PTR
- SOA:Start Of Authority,起始授权记录;一个区域解析库有且仅能有一个SOA记录,且必须位于解析库的第一条
- A:IPv4 正向解析资源记录
- AAAA:IPv6正向解析资源记录
- NS:用于标注当前区域的DNS服务器
- CNAME:别名记录
- MX:邮件交换器
- TXT:对域名进行标识说明的一种方式,一般做验证记录会使用此项,如SPF(反垃圾邮件)记录,https验证 登
- PTR:
3.1、资源记录定义格式
name [TTL] IN rr_type value
使用@符号可引用当前区域名字
TTL 可以从全局继承
IN值可以通过继承上一条记录忽略不写
同一个名字可以通过多条记录定义多个值,此时DNS服务器会以轮询方式响应
同一个值也可能有多个不同定义的名字,通过多个名字指向同一个值进行定义,此时表示通过多个不同的名字找到同一台主机
3.2、SOA 记录
name:当前区域的名字
value:多个内容组成
当前主DNS服务器的FQDN,也可以使用当前区域的名字
当前区域的管理员邮箱,由于无法使用@符合,通常使用.替换,例如:root.janzen.com (root@janzen.com)
主从服务区域传输相关定义以及否定答案的统一TTL设置
@ IN SOA dns1.janzen.com root.janzen.com ( 1 ; 序列号 604800 ; 刷新时间 86400 ; 重试时间 2419200 ; 过期时间 604800 ) ; 否定答案的TTL值
3.3、A记录
name:主机的FQDN,可以.结尾代表完整名称,也可以简写末尾不加.
value:对应的IPv4地址
dns1 A 10.0.0.20dns2 A 10.0.0.21gitlab.janzen.com. A 10.0.0.13harbor A 10.0.0.9harbor A 10.0.0.10
3.4、AAAA记录
name:主机的FQDN,可以.结尾代表完整名称,也可以简写末尾不加.
value:对应的IPv6地址
3.5、NS记录
name:当前区域的名字
value:当前区域某DNS服务器的名字
相邻的两个资源记录name相同时,后续的可以省略
对于NS记录而言,每一条NS记录后面的名字,后续都应该有一条对应的A记录
一个区域可以有多条NS记录
@ IN NS dns1 NS dns2
3.6、CNAME记录
name:别名FQDN
value:真实的FQDN
dns IN CNAME dns1
3.7、MX记录
name:当前区域的名字
value:当前区域某邮件服务器(smtp服务器)的名字
一个区域内,MX记录可以有多个,但每个记录的value后面都应该有一个(0-99)数字,表示此服务器的优先级
对于MX记录而言,每一条NS记录后面的名字,后续都应该有一条对应的A记录
@ IN MX 12 mail1 IN MX 10 mail2mail1 IN A 10.0.0.31mail2 IN A 10.0.0.32
3.8、TXT记录
name:文本描述头
value:文本内容
_dnstxt TXT this is @ name server
3.9、PTR记录
name:IP
value:FQDN
name的IP拥有固定写法,需要将IP反向书写,并添加特殊后缀 in-addr.arpa.
完整写法为:20.0.0.10.in-addr.arpa.
网络地址及后缀可以省略,主机地址依旧要反写
20.0.0.10.in-addr.arpa. IN PTR dns.janzen.com.#由于 10.0.0 为网络地址,可以省略 9 IN PTR harbor.janzen.com.
三、DNS工具介绍
dig 工具介绍
用于测试DNS解析结果
Usage: dig [@global-server] [domain] [q-type] [q-class] {q-opt}Where: domain is in the Domain Name System q-class is one of (in,hs,ch,...) [default: in] q-type is one of (a,any,mx,ns,soa,hinfo,axfr,txt,...) [default:a] (Use ixfr=version for type ixfr) q-opt +[no]trace (Trace delegation down from root [+dnssec]) +[no]recurse (Recursive mode (+[no]rdflag))#获取目标dns全部解析记录dig -tAXFR janzen.com @10.0.0.21#跟踪域名解析路径dig +trace app3.janzen.com @10.0.0.21#查询PTR记录dig -x 10.0.0.21#直接显示域名查询结果dig +short app3.janzen.com @10.0.0.71
nslookup工具
nslookup [-option] [name | -] [server]
rndc DNS管理工具
Usage: rndc [-b address] [-c config] [-s server] [-p port] [-k key-file ] [-y key] [-r] [-V] commandcommand is one of the following: addzone zone [class [view]] { zone-options } Add zone to given view. Requires allow-new-zones option. delzone [-clean] zone [class [view]] Removes zone from given view. dnstap -reopen Close, truncate and re-open the DNSTAP output file. dnstap -roll count Close, rename and re-open the DNSTAP output file(s). dumpdb [-all|-cache|-zones|-adb|-bad|-fail] [view ...] Dump cache(s) to the dump file (named_dump.db). flush Flushes all of the server"s caches. flush [view] Flushes the server"s cache for a view. flushname name [view] Flush the given name from the server"s cache(s) flushtree name [view] Flush all names under the given name from the server"s cache(s) freeze Suspend updates to all dynamic zones. freeze zone [class [view]] Suspend updates to a dynamic zone. halt Stop the server without saving pending updates. halt -p Stop the server without saving pending updates reporting process id. loadkeys zone [class [view]] Update keys without signing immediately. managed-keys refresh [class [view]] Check trust anchor for RFC 5011 key changes managed-keys status [class [view]] Display RFC 5011 managed keys information managed-keys sync [class [view]] Write RFC 5011 managed keys to disk modzone zone [class [view]] { zone-options } Modify a zone"s configuration. Requires allow-new-zones option. notify zone [class [view]] Resend NOTIFY messages for the zone. notrace Set debugging level to 0. nta -dump List all negative trust anchors. nta [-lifetime duration] [-force] domain [view] Set a negative trust anchor, disabling DNSSEC validation for the given domain. Using -lifetime specifies the duration of the NTA, up to one week. Using -force prevents the NTA from expiring before its full lifetime, even if the domain can validate sooner. nta -remove domain [view] Remove a negative trust anchor, re-enabling validation for the given domain. querylog [ on | off ] Enable / disable query logging. reconfig Reload configuration file and new zones only. recursing Dump the queries that are currently recursing (named.recursing) refresh zone [class [view]] Schedule immediate maintenance for a zone. reload Reload configuration file and zones. reload zone [class [view]] Reload a single zone. retransfer zone [class [view]] Retransfer a single zone without checking serial number. scan Scan available network interfaces for changes. secroots [view ...] Write security roots to the secroots file. showzone zone [class [view]] Print a zone"s configuration. sign zone [class [view]] Update zone keys, and sign as needed. signing -clear all zone [class [view]] Remove the private records for all keys that have finished signing the given zone. signing -clear / zone [class [view]] Remove the private record that indicating the given key has finished signing the given zone. signing -list zone [class [view]] List the private records showing the state of DNSSEC signing in the given zone. signing -nsec3param hash flags iterations salt zone [class [view]] Add NSEC3 chain to zone if already signed. Prime zone with NSEC3 chain if not yet signed. signing -nsec3param none zone [class [view]] Remove NSEC3 chains from zone. signing -serial zone [class [view]] Set the zones"s serial to . stats Write server statistics to the statistics file. status Display status of the server. stop Save pending updates to master files and stop the server. stop -p Save pending updates to master files and stop the server reporting process id. sync [-clean] Dump changes to all dynamic zones to disk, and optionally remove their journal files. sync [-clean] zone [class [view]] Dump a single zone"s changes to disk, and optionally remove its journal file. thaw Enable updates to all dynamic zones and reload them. thaw zone [class [view]] Enable updates to a frozen dynamic zone and reload it. trace Increment debugging level by one. trace level Change the debugging level. tsig-delete keyname [view] Delete a TKEY-negotiated TSIG key. tsig-list List all currently active TSIG keys, including both statically configured and TKEY-negotiated keys. validation [ yes | no | status ] [view] Enable / disable DNSSEC validation. zonestatus zone [class [view]] Display the current status of a zone.Version: 9.11.3-1ubuntu1.18-Ubuntu 四、DNS安装部署
1、Centos7配置域名正向解析主服务器
1.1、yum安装bind服务,及DNS工具bind-utils
yum install -y bind bind-utils
1.2、修改 named.conf 配置文件,禁用服务限制,引入区域配置文件
[root@node-centos7-70 ~]# vim /etc/named.conf options { # listen-on port 53 { 127.0.0.1; }; listen-on-v6 port 53 { ::1; }; directory "/var/named"; dump-file "/var/named/data/cache_dump.db"; statistics-file "/var/named/data/named_stats.txt"; memstatistics-file "/var/named/data/named_mem_stats.txt"; recursing-file "/var/named/data/named.recursing"; secroots-file "/var/named/data/named.secroots"; # allow-query { localhost; }; recursion yes; dnssec-enable yes; dnssec-validation yes; /* Path to ISC DLV key */ bindkeys-file "/etc/named.root.key"; managed-keys-directory "/var/named/dynamic"; pid-file "/run/named/named.pid"; session-keyfile "/run/named/session.key";};logging { channel default_debug { file "data/named.run"; severity dynamic; };};zone "." IN { type hint; file "named.ca";};include "/etc/named.rfc1912.zones";include "/etc/named.root.key";include "/etc/named.zones"1.3、创建 named.zones 区域配置文件
[root@node-centos7-70 ~]# vim /etc/named.zoneszone "janzen.com" IN { type master; file "named.janzen.com"; allow-update { none; }; };1.4、创建 named.janzen.com 区域解析库文件
[root@node-centos7-70 etc]# vim /var/named/named.janzen.com;; BIND reverse data file for broadcast zone;$TTL 604800@ IN SOA janzen.com. root.localhost. ( 1 ; Serial 604800 ; Refresh 86400 ; Retry 2419200 ; Expire 604800 ) ; Negative Cache TTL;@ IN NS dns1 IN NS dns2 IN MX 12 mail1 IN MX 10 mail2dns IN CNAME dns1dns1 IN A 10.0.0.20dns2 IN A 10.0.0.21gitlab IN A 10.0.0.13harbor IN A 10.0.0.9harbor IN A 10.0.0.10www IN A 10.0.0.11mail1 IN A 10.0.0.31mail2 IN A 10.0.0.32_dnstext IN TXT this is @ name server
1.5、修改文件权限
[root@node-centos7-70 etc]# chmod 640 {/etc/named.zones,/var/named/named.janzen.com}[root@node-centos7-70 etc]# chgrp named {/etc/named.zones,/var/named/named.janzen.com}1.6、设置named服务开机自启动
[root@node-centos7-70 etc]# systemctl enable --now named
1.7、使用dig测试DNS服务
[root@node-centos7-70 etc]# dig dns.janzen.com @10.0.0.70; <<>> DiG 9.11.4-P2-RedHat-9.11.4-26.P2.el7_9.13 <<>> dns.janzen.com @10.0.0.70;; global options: +cmd;; Got answer:;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 51429;; flags: qr aa rd ra; QUERY: 1, ANSWER: 2, AUTHORITY: 2, ADDITIONAL: 2;; OPT PSEUDOSECTION:; EDNS: version: 0, flags:; udp: 4096;; QUESTION SECTION:;dns.janzen.com. IN A;; ANSWER SECTION:dns.janzen.com. 604800 IN CNAME dns1.janzen.com.dns1.janzen.com. 604800 IN A 10.0.0.20;; AUTHORITY SECTION:janzen.com. 604800 IN NS dns2.janzen.com.janzen.com. 604800 IN NS dns1.janzen.com.;; ADDITIONAL SECTION:dns2.janzen.com. 604800 IN A 10.0.0.21;; Query time: 0 msec;; SERVER: 10.0.0.70#53(10.0.0.70);; WHEN: 四 5月 25 18:16:54 CST 2023;; MSG SIZE rcvd: 127[root@node-centos7-70 etc]# dig janzen.com @10.0.0.70 mx; <<>> DiG 9.11.4-P2-RedHat-9.11.4-26.P2.el7_9.13 <<>> janzen.com @10.0.0.70 mx;; global options: +cmd;; Got answer:;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 2566;; flags: qr aa rd ra; QUERY: 1, ANSWER: 2, AUTHORITY: 2, ADDITIONAL: 5;; OPT PSEUDOSECTION:; EDNS: version: 0, flags:; udp: 4096;; QUESTION SECTION:;janzen.com. IN MX;; ANSWER SECTION:janzen.com. 604800 IN MX 10 mail2.janzen.com.janzen.com. 604800 IN MX 12 mail1.janzen.com.;; AUTHORITY SECTION:janzen.com. 604800 IN NS dns2.janzen.com.janzen.com. 604800 IN NS dns1.janzen.com.;; ADDITIONAL SECTION:mail1.janzen.com. 604800 IN A 10.0.0.31mail2.janzen.com. 604800 IN A 10.0.0.32dns1.janzen.com. 604800 IN A 10.0.0.20dns2.janzen.com. 604800 IN A 10.0.0.21;; Query time: 0 msec;; SERVER: 10.0.0.70#53(10.0.0.70);; WHEN: 四 5月 25 18:18:09 CST 2023;; MSG SIZE rcvd: 185[root@node-centos7-70 etc]# dig harbor.janzen.com @10.0.0.70; <<>> DiG 9.11.4-P2-RedHat-9.11.4-26.P2.el7_9.13 <<>> harbor.janzen.com @10.0.0.70;; global options: +cmd;; Got answer:;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 33334;; flags: qr aa rd ra; QUERY: 1, ANSWER: 2, AUTHORITY: 2, ADDITIONAL: 3;; OPT PSEUDOSECTION:; EDNS: version: 0, flags:; udp: 4096;; QUESTION SECTION:;harbor.janzen.com. IN A;; ANSWER SECTION:harbor.janzen.com. 604800 IN A 10.0.0.10harbor.janzen.com. 604800 IN A 10.0.0.9;; AUTHORITY SECTION:janzen.com. 604800 IN NS dns1.janzen.com.janzen.com. 604800 IN NS dns2.janzen.com.;; ADDITIONAL SECTION:dns1.janzen.com. 604800 IN A 10.0.0.20dns2.janzen.com. 604800 IN A 10.0.0.21;; Query time: 0 msec;; SERVER: 10.0.0.70#53(10.0.0.70);; WHEN: 四 5月 25 18:20:07 CST 2023;; MSG SIZE rcvd: 148
1.8、修改区域解析库文件内容,使用 rndc 重载配置
[root@node-centos7-70 etc]# vim /var/named/named.janzen.com $TTL 604800@ IN SOA janzen.com. root.localhost. ( 2 ; Serial 604800 ; Refresh 86400 ; Retry 2419200 ; Expire 604800 ) ; Negative Cache TTL@ IN NS dns1 IN NS dns2 IN MX 12 mail1 IN MX 10 mail2dns IN CNAME dns1dns1 IN A 10.0.0.70dns2 IN A 10.0.0.21gitlab IN A 10.0.0.13harbor IN A 10.0.0.9harbor IN A 10.0.0.10www IN A 10.0.0.11mail1 IN A 10.0.0.31mail2 IN A 10.0.0.32_dnstext IN TXT this is @ name server[root@node-centos7-70 etc]# rndc reloadserver reload successful
[root@node-centos7-70 etc]# dig dns.janzen.com @10.0.0.70; <<>> DiG 9.11.4-P2-RedHat-9.11.4-26.P2.el7_9.13 <<>> dns.janzen.com @10.0.0.70;; global options: +cmd;; Got answer:;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 5247;; flags: qr aa rd ra; QUERY: 1, ANSWER: 2, AUTHORITY: 2, ADDITIONAL: 2;; OPT PSEUDOSECTION:; EDNS: version: 0, flags:; udp: 4096;; QUESTION SECTION:;dns.janzen.com. IN A;; ANSWER SECTION:dns.janzen.com. 604800 IN CNAME dns1.janzen.com.dns1.janzen.com. 604800 IN A 10.0.0.70;; AUTHORITY SECTION:janzen.com. 604800 IN NS dns2.janzen.com.janzen.com. 604800 IN NS dns1.janzen.com.;; ADDITIONAL SECTION:dns2.janzen.com. 604800 IN A 10.0.0.21;; Query time: 0 msec;; SERVER: 10.0.0.70#53(10.0.0.70);; WHEN: 四 5月 25 18:27:45 CST 2023;; MSG SIZE rcvd: 127
2、Ubuntu apt安装bind服务
1.1、apt安装bind9服务,及DNS工具bind9utils
[root@Node-Ubuntu1804-20:~]# apt install -y bind9 bind9utils
1.2、修改 named.conf 配置文件,引入区域配置文件
[root@Node-Ubuntu1804-20:~]# cat /etc/bind/named.conf// This is the primary configuration file for the BIND DNS server named.//// Please read /usr/share/doc/bind9/README.Debian.gz for information on the // structure of BIND configuration files in Debian, *BEFORE* you customize // this configuration file.//// If you are just adding zones, please do that in /etc/bind/named.conf.localinclude "/etc/bind/named.conf.options";include "/etc/bind/named.conf.local";include "/etc/bind/named.conf.default-zones";include "/etc/bind/named.zones";
1.3、创建 named.zones 区域配置文件
[root@Node-Ubuntu1804-20:~]# vim /etc/bind/named.zoneszone janzen.com IN { type master; file "/etc/bind/db.janzen.com"; };1.4、创建 db.janzen.com 区域解析库文件
[root@Node-Ubuntu1804-20:~]# vim /etc/bind/db.janzen.com$TTL 604800 @ IN SOA janzen.com. root.localhost. ( 1 ; Serial 604800 ; Refresh 86400 ; Retry 2419200 ; Expire 604800 ) ; Negative Cache TTL@ IN NS dns1 IN NS dns2 IN MX 12 mail1 IN MX 10 mail2dns IN CNAME dns1dns1 IN A 10.0.0.20dns2 IN A 10.0.0.21gitlab IN A 10.0.0.13harbor IN A 10.0.0.9harbor IN A 10.0.0.10www IN A 10.0.0.11mail1 IN A 10.0.0.31mail2 IN A 10.0.0.32_dnstext IN TXT this is @ name server
1.5、修改文件权限
[root@Node-Ubuntu1804-20:~]# chmod 640 /etc/bind/{named.zones,db.janzen.com} [root@Node-Ubuntu1804-20:~]# chgrp bind /etc/bind/{named.zones,db.janzen.com}
1.6、启动 bind9 服务
[root@Node-Ubuntu1804-20:~]# systemctl start bind9
1.7、使用dig测试DNS服务
[root@Ansible-Ubuntu1804-25:~]# dig dns.janzen.com @10.0.0.20; <<>> DiG 9.11.3-1ubuntu1.18-Ubuntu <<>> dns.janzen.com @10.0.0.20;; global options: +cmd;; Got answer:;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 32150;; flags: qr aa rd ra; QUERY: 1, ANSWER: 2, AUTHORITY: 2, ADDITIONAL: 2;; OPT PSEUDOSECTION:; EDNS: version: 0, flags:; udp: 4096; COOKIE: 95d843b6344528dfc99349d4646f3bbb5812908fa82e3d3f (good);; QUESTION SECTION:;dns.janzen.com. IN A;; ANSWER SECTION:dns.janzen.com. 604800 IN CNAME dns1.janzen.com.dns1.janzen.com. 604800 IN A 10.0.0.20;; AUTHORITY SECTION:janzen.com. 604800 IN NS dns1.janzen.com.janzen.com. 604800 IN NS dns2.janzen.com.;; ADDITIONAL SECTION:dns2.janzen.com. 604800 IN A 10.0.0.21;; Query time: 0 msec;; SERVER: 10.0.0.20#53(10.0.0.20);; WHEN: Thu May 25 18:43:07 CST 2023;; MSG SIZE rcvd: 155
[root@Ansible-Ubuntu1804-25:~]# dig janzen.com @10.0.0.20 mx; <<>> DiG 9.11.3-1ubuntu1.18-Ubuntu <<>> janzen.com @10.0.0.20 mx;; global options: +cmd;; Got answer:;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 11520;; flags: qr aa rd ra; QUERY: 1, ANSWER: 2, AUTHORITY: 2, ADDITIONAL: 5;; OPT PSEUDOSECTION:; EDNS: version: 0, flags:; udp: 4096; COOKIE: 2bd0379cc8f4ca918c8ed28e646f3c5c2d56e5c3704f4752 (good);; QUESTION SECTION:;janzen.com. IN MX;; ANSWER SECTION:janzen.com. 604800 IN MX 10 mail2.janzen.com.janzen.com. 604800 IN MX 12 mail1.janzen.com.;; AUTHORITY SECTION:janzen.com. 604800 IN NS dns2.janzen.com.janzen.com. 604800 IN NS dns1.janzen.com.;; ADDITIONAL SECTION:mail2.janzen.com. 604800 IN A 10.0.0.32mail1.janzen.com. 604800 IN A 10.0.0.31dns1.janzen.com. 604800 IN A 10.0.0.20dns2.janzen.com. 604800 IN A 10.0.0.21;; Query time: 1 msec;; SERVER: 10.0.0.20#53(10.0.0.20);; WHEN: Thu May 25 18:45:48 CST 2023;; MSG SIZE rcvd: 213
[root@Ansible-Ubuntu1804-25:~]# dig harbor.janzen.com @10.0.0.20; <<>> DiG 9.11.3-1ubuntu1.18-Ubuntu <<>> harbor.janzen.com @10.0.0.20;; global options: +cmd;; Got answer:;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 45201;; flags: qr aa rd ra; QUERY: 1, ANSWER: 2, AUTHORITY: 2, ADDITIONAL: 3;; OPT PSEUDOSECTION:; EDNS: version: 0, flags:; udp: 4096; COOKIE: 97efe511ca506c99495a4d4d646f3c70aac936a36fab58f2 (good);; QUESTION SECTION:;harbor.janzen.com. IN A;; ANSWER SECTION:harbor.janzen.com. 604800 IN A 10.0.0.9harbor.janzen.com. 604800 IN A 10.0.0.10;; AUTHORITY SECTION:janzen.com. 604800 IN NS dns2.janzen.com.janzen.com. 604800 IN NS dns1.janzen.com.;; ADDITIONAL SECTION:dns1.janzen.com. 604800 IN A 10.0.0.20dns2.janzen.com. 604800 IN A 10.0.0.21;; Query time: 1 msec;; SERVER: 10.0.0.20#53(10.0.0.20);; WHEN: Thu May 25 18:46:08 CST 2023;; MSG SIZE rcvd: 176
1.8、修改区域解析库文件内容,使用 rndc 重载配置
[root@Node-Ubuntu1804-20:~]# vim /etc/bind/db.janzen.com$TTL 604800@ IN SOA janzen.com. root.localhost. ( 2 ; Serial 604800 ; Refresh 86400 ; Retry 2419200 ; Expire 604800 ) ; Negative Cache TTL@ IN NS dns1 IN NS dns2 IN NS dns3 IN MX 12 mail1 IN MX 10 mail2dns IN CNAME dns1dns1 IN A 10.0.0.20dns2 IN A 10.0.0.21dns3 IN A 10.0.0.70gitlab IN A 10.0.0.13harbor IN A 10.0.0.9harbor IN A 10.0.0.10www IN A 10.0.0.11mail1 IN A 10.0.0.31mail2 IN A 10.0.0.32_dnstext IN TXT this is @ name server[root@Node-Ubuntu1804-20:~]# rndc reload janzen.comzone reload queued
[root@Ansible-Ubuntu1804-25:~]# dig ns janzen.com @10.0.0.20; <<>> DiG 9.11.3-1ubuntu1.18-Ubuntu <<>> ns janzen.com @10.0.0.20;; global options: +cmd;; Got answer:;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 1374;; flags: qr aa rd ra; QUERY: 1, ANSWER: 3, AUTHORITY: 0, ADDITIONAL: 4;; OPT PSEUDOSECTION:; EDNS: version: 0, flags:; udp: 4096; COOKIE: f4619011881ac8168f1e6981646f3ce9f82e1484c3c43f22 (good);; QUESTION SECTION:;janzen.com. IN NS;; ANSWER SECTION:janzen.com. 604800 IN NS dns2.janzen.com.janzen.com. 604800 IN NS dns1.janzen.com.janzen.com. 604800 IN NS dns3.janzen.com.;; ADDITIONAL SECTION:dns1.janzen.com. 604800 IN A 10.0.0.20dns2.janzen.com. 604800 IN A 10.0.0.21dns3.janzen.com. 604800 IN A 10.0.0.70;; Query time: 0 msec;; SERVER: 10.0.0.20#53(10.0.0.20);; WHEN: Thu May 25 18:48:09 CST 2023;; MSG SIZE rcvd: 172
五、DNS反向解析配置
1、Centos7 配置反向解析
1.1、在 named.zones 中添加反向解析区域记录
[root@node-centos7-70 etc]# vim /etc/named.zones zone "janzen.com" IN { type master; file "named.janzen.com"; allow-update { none; }; };zone "0.0.10.in-addr.arpa" IN { type master; file "named.10.0.0"; };1.2、创建 named.10.0.0 区域反向解析库
[root@node-centos7-70 etc]# vim /var/named/named.10.0.0$TTL 604800@ IN SOA janzen.com. root.localhost. ( 2 ; Serial 604800 ; Refresh 86400 ; Retry 2419200 ; Expire 604800 ) ; Negative Cache TTL NS dns1.janzen.com.70 IN PTR dns1.janzen.com.21 IN PTR dns2.janzen.com.9 IN PTR harbor.janzen.com.10 IN PTR harbor.janzen.com.31 IN PTR mail1.janzen.com.32 IN PTR mail2.janzen.com.
1.3、重新加载服务
[root@node-centos7-70 etc]# rndc reloadserver reload successful
1.4、校验反向解析效果
[root@Node-Ubuntu1804-20:~]# dig -t ptr 9.0.0.10.in-addr.arpa. @10.0.0.70; <<>> DiG 9.11.3-1ubuntu1.18-Ubuntu <<>> -t ptr 9.0.0.10.in-addr.arpa. @10.0.0.70;; global options: +cmd;; Got answer:;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 17291;; flags: qr aa rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 1, ADDITIONAL: 2;; OPT PSEUDOSECTION:; EDNS: version: 0, flags:; udp: 4096; COOKIE: d92a9b9a0cba6df1281d8d7a646f4fe3ba882373c080d21e (good);; QUESTION SECTION:;9.0.0.10.in-addr.arpa. IN PTR;; ANSWER SECTION:9.0.0.10.in-addr.arpa. 604800 IN PTR harbor.janzen.com.;; AUTHORITY SECTION:0.0.10.in-addr.arpa. 604800 IN NS dns1.janzen.com.;; ADDITIONAL SECTION:dns1.janzen.com. 604800 IN A 10.0.0.70;; Query time: 0 msec;; SERVER: 10.0.0.70#53(10.0.0.70);; WHEN: Thu May 25 20:09:07 CST 2023;; MSG SIZE rcvd: 144[root@Node-Ubuntu1804-20:~]# dig -t ptr 31.0.0.10.in-addr.arpa. @10.0.0.70; <<>> DiG 9.11.3-1ubuntu1.18-Ubuntu <<>> -t ptr 31.0.0.10.in-addr.arpa. @10.0.0.70;; global options: +cmd;; Got answer:;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 40029;; flags: qr aa rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 1, ADDITIONAL: 2;; OPT PSEUDOSECTION:; EDNS: version: 0, flags:; udp: 4096; COOKIE: 96c1482be18e12c7c27f80ae646f4fe90a240b78bb3e6e6c (good);; QUESTION SECTION:;31.0.0.10.in-addr.arpa. IN PTR;; ANSWER SECTION:31.0.0.10.in-addr.arpa. 604800 IN PTR mail1.janzen.com.;; AUTHORITY SECTION:0.0.10.in-addr.arpa. 604800 IN NS dns1.janzen.com.;; ADDITIONAL SECTION:dns1.janzen.com. 604800 IN A 10.0.0.70;; Query time: 0 msec;; SERVER: 10.0.0.70#53(10.0.0.70);; WHEN: Thu May 25 20:09:13 CST 2023;; MSG SIZE rcvd: 144
2、Ubuntu 配置反向解析
2.1、在 named.zones 中添加反向解析区域记录
[root@Node-Ubuntu1804-20:~]# vim /etc/bind/named.zones zone janzen.com IN { type master; file "/etc/bind/db.janzen.com"; }; zone "0.0.10.in-addr.arpa" IN { type master; file "/etc/bind/db.10.0.0"; };2.2、创建区域反向解析库
[root@Node-Ubuntu1804-20:~]# vim /etc/bind/db.10.0.0$TTL 604800@ IN SOA @ root.janzen.com. ( 1 ; Serial 604800 ; Refresh 86400 ; Retry 2419200 ; Expire 604800 ) ; Negative Cache TTL NS dns1.janzen.com. NS dns2.janzen.com. NS dns3.janzen.com. 20 IN PTR dns1.janzen.com.21 IN PTR dns2.janzen.com.70 IN PTR dns3.janzen.com.9 IN PTR harbor.janzen.com.10 IN PTR harbor.janzen.com.31 IN PTR mail1.janzen.com.32 IN PTR mail2.janzen.com.~
2.3、重新加载服务
[root@Node-Ubuntu1804-20:~]# rndc reloadserver reload successful
2.4、验证反向解析结果
[root@Ansible-Ubuntu1804-25:~]# dig -t ptr 20.0.0.10.in-addr.arpa. @10.0.0.20; <<>> DiG 9.11.3-1ubuntu1.18-Ubuntu <<>> -t ptr 20.0.0.10.in-addr.arpa. @10.0.0.20;; global options: +cmd;; Got answer:;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 30257;; flags: qr aa rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 3, ADDITIONAL: 4;; OPT PSEUDOSECTION:; EDNS: version: 0, flags:; udp: 4096; COOKIE: 84ac957d868c866b33777194646f52bc2f65ef3bae2f140f (good);; QUESTION SECTION:;20.0.0.10.in-addr.arpa. IN PTR;; ANSWER SECTION:20.0.0.10.in-addr.arpa. 604800 IN PTR dns1.janzen.com.;; AUTHORITY SECTION:0.0.10.in-addr.arpa. 604800 IN NS dns1.janzen.com.0.0.10.in-addr.arpa. 604800 IN NS dns3.janzen.com.0.0.10.in-addr.arpa. 604800 IN NS dns2.janzen.com.;; ADDITIONAL SECTION:dns1.janzen.com. 604800 IN A 10.0.0.20dns2.janzen.com. 604800 IN A 10.0.0.21dns3.janzen.com. 604800 IN A 10.0.0.70;; Query time: 0 msec;; SERVER: 10.0.0.20#53(10.0.0.20);; WHEN: Thu May 25 20:21:17 CST 2023;; MSG SIZE rcvd: 208[root@Ansible-Ubuntu1804-25:~]# dig -t ptr 70.0.0.10.in-addr.arpa. @10.0.0.20; <<>> DiG 9.11.3-1ubuntu1.18-Ubuntu <<>> -t ptr 70.0.0.10.in-addr.arpa. @10.0.0.20;; global options: +cmd;; Got answer:;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 28274;; flags: qr aa rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 3, ADDITIONAL: 4;; OPT PSEUDOSECTION:; EDNS: version: 0, flags:; udp: 4096; COOKIE: cb50d5bc319d559d22178c59646f52c728e60ab6e3f06ad3 (good);; QUESTION SECTION:;70.0.0.10.in-addr.arpa. IN PTR;; ANSWER SECTION:70.0.0.10.in-addr.arpa. 604800 IN PTR dns3.janzen.com.;; AUTHORITY SECTION:0.0.10.in-addr.arpa. 604800 IN NS dns2.janzen.com.0.0.10.in-addr.arpa. 604800 IN NS dns3.janzen.com.0.0.10.in-addr.arpa. 604800 IN NS dns1.janzen.com.;; ADDITIONAL SECTION:dns1.janzen.com. 604800 IN A 10.0.0.20dns2.janzen.com. 604800 IN A 10.0.0.21dns3.janzen.com. 604800 IN A 10.0.0.70;; Query time: 0 msec;; SERVER: 10.0.0.20#53(10.0.0.20);; WHEN: Thu May 25 20:21:27 CST 2023;; MSG SIZE rcvd: 208
六、DNS主从架构部署
1、Centos7 主从架构配置
1.1、主服务器配置
[root@node-centos7-70 etc]# vim /etc/named.conf //// named.conf//// Provided by Red Hat bind package to configure the ISC BIND named(8) DNS// server as a caching only nameserver (as a localhost DNS resolver only).//// See /usr/share/doc/bind*/sample/ for example named configuration files.//// See the BIND Administrator"s Reference Manual (ARM) for details about the// configuration located in /usr/share/doc/bind-{version}/Bv9ARM.htmloptions { # listen-on port 53 { 127.0.0.1; }; listen-on-v6 port 53 { ::1; }; directory "/var/named"; dump-file "/var/named/data/cache_dump.db"; statistics-file "/var/named/data/named_stats.txt"; memstatistics-file "/var/named/data/named_mem_stats.txt"; recursing-file "/var/named/data/named.recursing"; secroots-file "/var/named/data/named.secroots"; # allow-query { localhost; }; allow-transfer { none; }; /* - If you are building an AUTHORITATIVE DNS server, do NOT enable recursion. - If you are building a RECURSIVE (caching) DNS server, you need to enable recursion. - If your recursive DNS server has a public IP address, you MUST enable access control to limit queries to your legitimate users. Failing to do so will cause your server to become part of large scale DNS amplification attacks. Implementing BCP38 within your network would greatly reduce such attack surface */ recursion yes; dnssec-enable yes; dnssec-validation yes; /* Path to ISC DLV key */ bindkeys-file "/etc/named.root.key"; managed-keys-directory "/var/named/dynamic"; pid-file "/run/named/named.pid"; session-keyfile "/run/named/session.key";};logging { channel default_debug { file "data/named.run"; severity dynamic; };};zone "." IN { type hint; file "named.ca";};include "/etc/named.rfc1912.zones";include "/etc/named.root.key";include "/etc/named.zones";[root@node-centos7-70 etc]# vim /etc/named.zones zone "janzen.com" IN { type master; file "named.janzen.com"; allow-update { none; }; allow-transfer { 10.0.0.71; }; };zone "0.0.10.in-addr.arpa" IN { type master; file "named.10.0.0"; };1.2、从服务器配置
[root@node-centos7-71 ~]# vim /etc/named.conf //// named.conf//// Provided by Red Hat bind package to configure the ISC BIND named(8) DNS// server as a caching only nameserver (as a localhost DNS resolver only).//// See /usr/share/doc/bind*/sample/ for example named configuration files.//// See the BIND Administrator"s Reference Manual (ARM) for details about the// configuration located in /usr/share/doc/bind-{version}/Bv9ARM.htmloptions { # listen-on port 53 { 127.0.0.1; }; listen-on-v6 port 53 { ::1; }; directory "/var/named"; dump-file "/var/named/data/cache_dump.db"; statistics-file "/var/named/data/named_stats.txt"; memstatistics-file "/var/named/data/named_mem_stats.txt"; recursing-file "/var/named/data/named.recursing"; secroots-file "/var/named/data/named.secroots"; # allow-query { localhost; }; allow-tranfer { none; }; /* - If you are building an AUTHORITATIVE DNS server, do NOT enable recursion. - If you are building a RECURSIVE (caching) DNS server, you need to enable recursion. - If your recursive DNS server has a public IP address, you MUST enable access control to limit queries to your legitimate users. Failing to do so will cause your server to become part of large scale DNS amplification attacks. Implementing BCP38 within your network would greatly reduce such attack surface */ recursion yes; dnssec-enable yes; dnssec-validation yes; /* Path to ISC DLV key */ bindkeys-file "/etc/named.root.key"; managed-keys-directory "/var/named/dynamic"; pid-file "/run/named/named.pid"; session-keyfile "/run/named/session.key";};logging { channel default_debug { file "data/named.run"; severity dynamic; };};zone "." IN { type hint; file "named.ca";};include "/etc/named.rfc1912.zones";include "/etc/named.root.key";include "/etc/named.zones";[root@node-centos7-71 ~]# vim /etc/named.zones zone "janzen.com" IN { type slave; file "slaves/named.janzen.com.slave"; masters { 10.0.0.70; } };2、Ubuntu 主从架构配置
2.1、主服务器配置
[root@Node-Ubuntu1804-20:~]# cat /etc/bind/named.conf | grep -v ^$ | grep -v ".*//"include "/etc/bind/named.conf.options";include "/etc/bind/named.conf.local";include "/etc/bind/named.conf.default-zones";include "/etc/bind/named.zones";[root@Node-Ubuntu1804-20:~]# cat /etc/bind/named.conf.options | grep -v ^$ | grep -v ".*//"options { directory "/var/cache/bind"; dnssec-validation auto; auth-nxdomain no; # conform to RFC1035 listen-on-v6 { any; }; allow-transfer { none; };};[root@Node-Ubuntu1804-20:~]# cat /etc/bind/named.zones zone janzen.com IN { type master; file "/etc/bind/db.janzen.com"; allow-transfer { 10.0.0.21; }; also-notify { 10.0.0.21; }; };2.2、从服务器配置
[root@Node-Ubuntu1804-21:~]# cat /etc/bind/named.conf | grep -v ^$ | grep -v ".*//"include "/etc/bind/named.conf.options";include "/etc/bind/named.conf.local";include "/etc/bind/named.conf.default-zones";include "/etc/bind/named.zones";[root@Node-Ubuntu1804-21:~]# cat /etc/bind/named.conf.options | grep -v ^$ | grep -v ".*//"options { directory "/var/cache/bind"; dnssec-validation auto; auth-nxdomain no; # conform to RFC1035 listen-on-v6 { any; }; allow-transfer { none; };};[root@Node-Ubuntu1804-21:~]# cat /etc/bind/named.zones zone janzen.com IN { type slave; file "/etc/bind/db.janzen.com.slave"; masters { 10.0.0.20; }; };七、DNS转发配置
1、Centos7 转发服务器配置
1.1、全局转发
[root@node-centos7-71 ~]# cat /etc/named.conf | grep -v ^$ | grep -v ".*//"options { listen-on-v6 port 53 { ::1; }; directory "/var/named"; dump-file "/var/named/data/cache_dump.db"; statistics-file "/var/named/data/named_stats.txt"; memstatistics-file "/var/named/data/named_mem_stats.txt"; recursing-file "/var/named/data/named.recursing"; secroots-file "/var/named/data/named.secroots"; allow-transfer { none; }; forward first; forwarders {10.0.0.70;}; /* - If you are building an AUTHORITATIVE DNS server, do NOT enable recursion. - If you are building a RECURSIVE (caching) DNS server, you need to enable recursion. - If your recursive DNS server has a public IP address, you MUST enable access control to limit queries to your legitimate users. Failing to do so will cause your server to become part of large scale DNS amplification attacks. Implementing BCP38 within your network would greatly reduce such attack surface */ recursion yes; dnssec-enable yes; dnssec-validation yes; /* Path to ISC DLV key */ bindkeys-file "/etc/named.root.key"; managed-keys-directory "/var/named/dynamic"; pid-file "/run/named/named.pid"; session-keyfile "/run/named/session.key";};logging { channel default_debug { file "data/named.run"; severity dynamic; };};zone "." IN { type hint; file "named.ca";};include "/etc/named.rfc1912.zones";include "/etc/named.root.key";include "/etc/named.zones";1.2、指定域转发
[root@node-centos7-71 ~]# cat /etc/named.zones zone janzen.cn IN { type forward; forward only; forwarders { 10.0.0.70; }; };2、Ubuntu 转发服务器配置
2.1、全局转发
[root@Node-Ubuntu1804-21:~]# cat /etc/bind/named.conf.options | grep -v ^$ | grep -v ".*//"options { directory "/var/cache/bind"; forward first; forwarders { 10.0.0.20; }; dnssec-validation auto; auth-nxdomain no; # conform to RFC1035 listen-on-v6 { any; }; allow-transfer { none; };};2.2、指定域转发
[root@Node-Ubuntu1804-21:~]# cat /etc/bind/named.zones | grep -v ^$ | grep -v ".*//"zone janzen.cn IN { type forward; forward only; forwarders { 10.0.0.20; }; }; 关键词:
-

-

-

-

【DNS】域名服务 Bind实现
ASP.NET Core MVC 从入门到精通之自动映射(二)-独家焦点
实时焦点:不是我说 iPhone拍照怎么就像富士相机了?
世界热推荐:NVIDIA黄仁勋:我们从未忘记游戏玩家!
号称使用AI独立管理基金的私募改口了:AI并非主要用于交易 热点
人间第一情歌词完整版原唱_人间第一情歌词|全球看热讯
实时焦点:今金贷最新退付消息:2023年兑付最新声明退付通知(退付进展告知)
曝华为版ChatGPT将下月发布 名为“盘古Chat”-当前独家
每日热议!128秒回顾中国载人航天高燃时刻:杨利伟 居功至伟!
【环球报资讯】假鸡翅怎么做法?
Web安全-渗透测试-基础知识02
Web安全-渗透测试-基础知识01-环球视点
撼迅AMD显卡抹错硅脂 温度高达110℃!曝生产线自证清白
MPV无敌手 比亚迪赵长江:腾势D9月销将达1.5万-每日看点
专访:美国没有资格充当民主人权教师爷——访俄政治学家米尔扎扬-世界热消息
可提速400公里!成渝中线高铁两大隧道同时进洞
天涯老用户自救 结果一地鸡毛:情怀 是最不值钱的东西
24点结束 腾讯视频VIP年卡+京东PLUS年卡138元 环球热门
十字军东征——现代社会可能重演吗?
文心一言 VS 讯飞星火 VS chatgpt (31)-- 算法导论5.2 3题 全球简讯
【奶奶看了都会】云服务器ChatGLM模型fine-tuning微调,让你拥有自己的知识库|世界动态
京东手机金榜出炉:Redmi K60力压iPhone 14夺冠
韧性回弹 脚感澎湃 361°运动拖鞋63元狂促(门店159元)-实时
真正的国产显卡之光!摩尔线程国产GPU、AI与元宇宙多项进展深入解读
中国铁塔:每天为近百万外卖和快递小哥提供换电充电服务
h2o2摩尔质量_h2o2
抢收同时抢种,河南已完成夏播2340万亩
华擎又出妖板!迷你身材 塞进去128个Arm核心 环球热资讯
多国出现人类偏肺病毒感染 一年1.6万儿童死亡!尚无治疗药物
自我的创建
ASP.NET Core 全局异常处理 世界热资讯
世界热门:(ex)BSGS/(扩展)大步小步算法 学习笔记
机会越来越好-与君周末谈20230604
虚幻5国漫巅峰 《斗罗大陆》比比东成神 巨型镰刀秒杀唐三
甚至没动工!《赛博朋克2077》续作明年才将投入开发 播资讯
我的脸被隐翅虫毁容了!千万小心“会飞的硫酸”
积成电子:预中标1.05亿元国家电网采购项目_世界新消息
全球微资讯!时速133严重车祸 车主:感谢驱逐舰05救我一命 又买了辆比亚迪汉
环球热文:马斯克北京首日晚宴多少钱?22人“吃”掉4.5万元
Web安全-渗透测试-基础知识01 世界播资讯
【天天速看料】Leetcode 1156. 单字符重复子串的最大长度
CPU的功能是什么_cpu的主要功能
网友把苹果封死水里一年 打开后水面飘了一层“巧克力”|每日时讯
PS造假神了!_热点评
读改变未来的九大算法笔记03_纠错码
当前报道:《安富莱嵌入式周报》第314期:微软推出开源DeviceScript编程语言适合低资源单片机,开源色度计,超声波穿戴设备,USB-C交换机,CMSIS
京东太狠:100W数据去重,用distinct还是group by,说说理由? 每日速讯
天天滚动:Spring整合mybatis使用xml配置事务
ChatGPT 国内镜像网站独家汇总:发现最优秀的人工智能对话体验!
小娜再见!微软宣布:Win10、Win11将正式抛弃Cortana 全球热点
观点:不打算修!AMD EPYC Rome服务器芯片运行1044天必定死机
全球量产车最低风阻!昊铂Hyper GT本月上市:能耗比Model 3还低|视点
世界最牛计算机课程变样了:接受AI改造
世界聚焦:Codeforces Round 876 (Div. 2)题解
姑姑拍到侄女做梦吃雪糕:画面分分钟萌翻
今头条!比亚迪突然上调车辆保养价格 部分车型涨幅达50%
【世界快播报】女子考科三系错安全带考官面如死灰:“交杯带”看无奈了
小娜再见!微软宣布:Win10、Win11将正式抛弃Cortana
汽车电动座椅原理_你知道吗|当前时讯
全球今热点:大量安卓用户逃离换iPhone:Android 13保有量不足15%
世界观速讯丨70万买红旗电动车 2年内修10次!车主退车遭拒:已修好无法退
劝学译文翻译_劝学译文
下水10秒即可感染 钻进皮肤体内生长!南京疾控提醒预防血吸虫病
世界简讯:1.2万元拍下单颗荔枝 男子:要送给女友
神速!这类品种再迎新成员,两大公募巨头助阵,对应ETF规模超870亿元_天天报资讯
焦点快看:男子路遇纸片鸟 一查竟是国保动物黄苇鳽:性格机警
QQ音乐豪华绿钻续费价格上调:连续包年158元 你续费吗?
速看:正版cd碟专卖店价格(正版cd碟专卖店)
微控制器实时操作系统实践1实时系统介绍 每日聚焦
全球消息!linux 性能自我学习 ———— cpu 快速定位问题 [六]
苹果语音助手功能将重大升级:Hey Siri成历史
3分钟回顾神十五航天员返回全程:遇上绝美日出朝霞
林峰交往过的女朋友(林峰女朋友)
MES系统初探(一)|世界最资讯
【环球财经】美国总统拜登签署债务上限法案
丰田反对电动车:建议别反对|环球观速讯
平均年龄最大的航天员乘组“落地” 神舟十五号载人飞行任务圆满成功 焦点快播
三星全球首款8K电竞显示器8月上市:用上TCL华星国产高端57英寸屏-世界今日讯
天天日报丨中国战舰果敢拦阻穿越台湾海峡的美国和加拿大海军舰艇
存储价格被国产干碎 大厂密谋涨价:2TB该抄底了
【全球播资讯】最多领1600元!北京发放新一批消费券:手机、电脑等都能用
《蜘蛛侠:纵横宇宙》票房超预期_当前热文
地图的三要素有哪些?_地图的三要素是什么 _3分
俄罗斯呼吁本国iPhone用户彻查手机 存在后门:苹果回应永远不会
【天天聚看点】太空出差186天!神十五乘组返回地球:成功着陆
今年前4个月沈阳市快递业务收入25.67亿元 环球时讯
新能源汽修人才缺口或达80%:汽修学员走出校门就进厂-焦点短讯
环球观焦点:苹果和安卓厂商为何都放弃了小屏市场?幕后原因揭晓
苹果头显来了:难成下一个“iPhone”
4个月卖1751.5亿 彩票盯上年轻人?专家提醒不能靠彩票发财 中奖率低
上海长兴岛房价最新走势_上海长兴岛房价
多彩网安入选第三届贵州省网络安全应急技术支撑单位
世界热讯:智齿是什么意思?_智齿是什么意思
焦点热议:致远的意思解释词语(致远的意思)
焦点速递!3099元起 vivo S17 Pro下周首销:影像比肩高端旗舰
网易云盘的歌怎样分享_网易云盘
环球简讯:神舟十五号载人飞船撤离空间站
每日视点!向安卓看齐!iOS 17下周发:开放第三方应用商店
天天热资讯!一年跌价超95% 只花38元华为P50 Pro秒变5G手机
环球观热点:上海两车“斗气” 致一车骑跨高架栏:专家喊话司机要跳出吃亏思维 吃亏是福