最新要闻
- 动态:3.8节大促:腾讯视频、QQ、绿钻、B站、百度网盘会员五折起
- 看点:钢琴弹出的声音怎么这么好听啊?离不开这四大件!
- 我国多地将体验超前温暖:郑州要破29℃ 但秋裤还不能脱
- 环球速看:当下最完美全面屏!京东方宣布独家供应努比亚Z50 Ultra
- 丧心病狂!这些人利用AI声音冒充亲人诈骗1100万美元
- 快看点丨8个月宝宝像打冷颤一样头抖_婴儿偶尔腿打颤正常吗
- 被批恶俗烂梗 鸡你太美商标无一注册成功:超20枚被判无效
- 即时看!AMD Yes!FSR 2.2插件已适用于虚幻引擎
- 环球焦点!V12自吸发动机+三电机!兰博基尼旗舰跑车动力信息公布:超千匹
- 天天即时看!招不到人!新加坡软件工程师月薪基本都超4.6万 跑不赢房租
- 微动态丨今晚打老虎!周杰伦用《赌侠2》梗回应周星驰喊话
- 焦点消息!2999元起!五菱羚羊智能电动自行车发布:新国标 200km续航
- 天猫超级红包开抢:今晚抢30万个6.8元天猫红包 最高3888元
- 观速讯丨育碧“壮士断腕”:将对欧洲工作室实施战略重组
- 天天热资讯!人民网评论:别让恶俗网络烂梗毒害孩子 散发恶臭气息
- 观速讯丨Win11强制要求的金身告破 TPM 2.0漏洞影响数十亿设备
手机

iphone11大小尺寸是多少?苹果iPhone11和iPhone13的区别是什么?
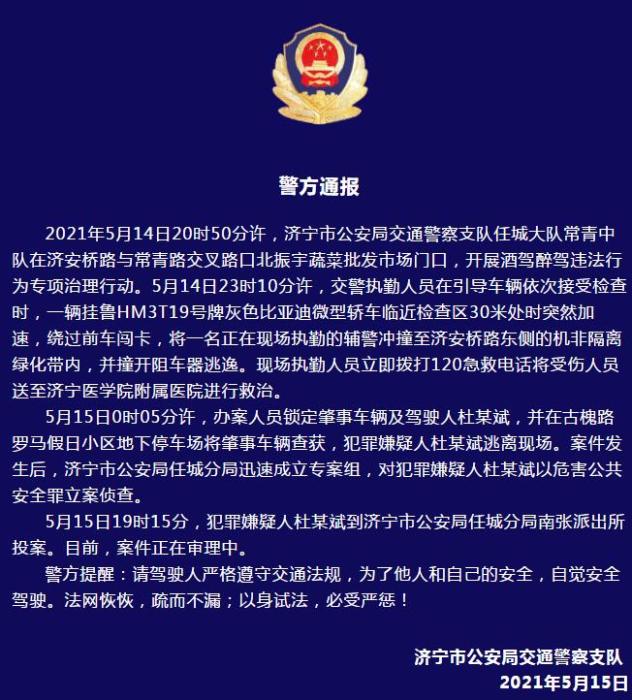
警方通报辅警执法直播中被撞飞:犯罪嫌疑人已投案
- iphone11大小尺寸是多少?苹果iPhone11和iPhone13的区别是什么?
- 警方通报辅警执法直播中被撞飞:犯罪嫌疑人已投案
- 男子被关545天申国赔:获赔18万多 驳回精神抚慰金
- 3天内26名本土感染者,辽宁确诊人数已超安徽
- 广西柳州一男子因纠纷杀害三人后自首
- 洱海坠机4名机组人员被批准为烈士 数千干部群众悼念
家电
今日热门!k8s对外服务之Ingress
一、Ingress理论
1.1Ingress简介
service的作用体现在两个方面,对集群内部,它不断跟踪pod的变化,更新endpoint中对应pod的对象,提供了ip不断变化的pod的服务发现机制;对集群外部,他类似负载均衡器,可以在集群内外部对pod进行访问。
在Kubernetes中,Pod的IP地址和service的ClusterIP仅可以在集群网络内部使用,对于集群外的应用是不可见的。为了使外部的应用能够访问集群内的服务,Kubernetes目前提供了以下几种方案:●NodePort:将service暴露在节点网络上,NodePort背后就是Kube-Proxy,Kube-Proxy是沟通service网络、Pod网络和节点网络的桥梁。测试环境使用还行,当有几十上百的服务在集群中运行时,NodePort的端口管理就是个灾难。因为每个端口只能是一种服务,端口范围只能是 30000-32767。
 (资料图片)
(资料图片)
●LoadBalancer:通过设置LoadBalancer映射到云服务商提供的LoadBalancer地址。这种用法仅用于在公有云服务提供商的云平台上设置 Service 的场景。受限于云平台,且通常在云平台部署LoadBalancer还需要额外的费用。在service提交后,Kubernetes就会调用CloudProvider在公有云上为你创建一个负载均衡服务,并且把被代理的Pod的IP地址配置给负载均衡服务做后端。
●externalIPs:service允许为其分配外部IP,如果外部IP路由到集群中一个或多个Node上,Service会被暴露给这些externalIPs。通过外部IP进入到集群的流量,将会被路由到Service的Endpoint上。
●Ingress:只需一个或者少量的公网IP和LB,即可同时将多个HTTP服务暴露到外网,七层反向代理。可以简单理解为service的service,它其实就是一组基于域名和URL路径,把用户的请求转发到一个或多个service的规则。
1.2Ingress组成
●ingress:ingress是一个API对象,通过yaml文件来配置,ingress对象的作用是定义请求如何转发到service的规则,可以理解为配置模板。ingress通过http或https暴露集群内部service,给service提供外部URL、负载均衡、SSL/TLS能力以及基于域名的反向代理。ingress要依靠 ingress-controller 来具体实现以上功能。
●ingress-controller:ingress-controller是具体实现反向代理及负载均衡的程序,对ingress定义的规则进行解析,根据配置的规则来实现请求转发。ingress-controller并不是k8s自带的组件,实际上ingress-controller只是一个统称,用户可以选择不同的ingress-controller实现,目前,由k8s维护的ingress-controller只有google云的GCE与ingress-nginx两个,其他还有很多第三方维护的ingress-controller,具体可以参考官方文档。但是不管哪一种ingress-controller,实现的机制都大同小异,只是在具体配置上有差异。一般来说,ingress-controller的形式都是一个pod,里面跑着daemon程序和反向代理程序。daemon负责不断监控集群的变化,根据 ingress对象生成配置并应用新配置到反向代理,比如ingress-nginx就是动态生成nginx配置,动态更新upstream,并在需要的时候reload程序应用新配置。为了方便,后面的例子都以k8s官方维护的ingress-nginx为例。
Ingress-Nginx github 地址:https://github.com/kubernetes/ingress-nginxIngress-Nginx 官方网站:https://kubernetes.github.io/ingress-nginx/
总结:ingress-controller才是负责具体转发的组件,通过各种方式将它暴露在集群入口,外部对集群的请求流量会先到 ingress-controller, 而ingress对象是用来告诉ingress-controller该如何转发请求,比如哪些域名、哪些URL要转发到哪些service等等。
1.3Ingress工作原理
(1)ingress-controller通过和 kubernetes APIServer 交互,动态的去感知集群中ingress规则变化,(2)然后读取它,按照自定义的规则,规则就是写明了哪个域名对应哪个service,生成一段nginx配置,(3)再写到nginx-ingress-controller的pod里,这个ingress-controller的pod里运行着一个Nginx服务,控制器会把生成的 nginx配置写入 /etc/nginx.conf文件中,(4)然后reload一下使配置生效。以此达到域名区分配置和动态更新的作用。
二、Ingress部署
2.1部署 nginx-ingress-controller
1、部署ingress-controller pod及相关资源
mkdir /opt/ingresscd /opt/ingress
官方下载地址:
wget https://raw.githubusercontent.com/kubernetes/ingress-nginx/nginx-0.25.0/deploy/static/mandatory.yaml
上面可能无法下载,可用国内的 gitee
wget https://gitee.com/mirrors/ingress-nginx/raw/nginx-0.25.0/deploy/static/mandatory.yamlwget https://gitee.com/mirrors/ingress-nginx/raw/nginx-0.30.0/deploy/static/mandatory.yaml
#mandatory.yaml文件中包含了很多资源的创建,包括namespace、ConfigMap、role,ServiceAccount等等所有部署ingress-controller需要的资源。
2.2修改 ClusterRole 资源配置
vim mandatory.yaml......apiVersion: rbac.authorization.k8s.io/v1beta1#RBAC相关资源从1.17版本开始改用rbac.authorization.k8s.io/v1,rbac.authorization.k8s.io/v1beta1在1.22版本即将弃用kind: ClusterRolemetadata: name: nginx-ingress-clusterrole labels: app.kubernetes.io/name: ingress-nginx app.kubernetes.io/part-of: ingress-nginxrules: - apiGroups: - "" resources: - configmaps - endpoints - nodes - pods - secrets verbs: - list - watch - apiGroups: - "" resources: - nodes verbs: - get - apiGroups: - "" resources: - services verbs: - get - list - watch - apiGroups: - "extensions" - "networking.k8s.io" # (0.25版本)增加 networking.k8s.io Ingress 资源的 api resources: - ingresses verbs: - get - list - watch - apiGroups: - "" resources: - events verbs: - create - patch - apiGroups: - "extensions" - "networking.k8s.io" # (0.25版本)增加 networking.k8s.io/v1 Ingress 资源的 api resources: - ingresses/status verbs: - update
//ingress 暴露服务的方式●方式一:Deployment+LoadBalancer 模式的 Service如果要把ingress部署在公有云,那用这种方式比较合适。用Deployment部署ingress-controller,创建一个 type为 LoadBalancer 的 service 关联这组 pod。大部分公有云,都会为 LoadBalancer 的 service 自动创建一个负载均衡器,通常还绑定了公网地址。 只要把域名解析指向该地址,就实现了集群服务的对外暴露
●方式二:DaemonSet+HostNetwork+nodeSelector用DaemonSet结合nodeselector来部署ingress-controller到特定的node上,然后使用HostNetwork直接把该pod与宿主机node的网络打通,直接使用宿主机的80/433端口就能访问服务。这时,ingress-controller所在的node机器就很类似传统架构的边缘节点,比如机房入口的nginx服务器。该方式整个请求链路最简单,性能相对NodePort模式更好。缺点是由于直接利用宿主机节点的网络和端口,一个node只能部署一个ingress-controller pod。 比较适合大并发的生产环境使用。
●方式三:Deployment+NodePort模式的Service同样用deployment模式部署ingress-controller,并创建对应的service,但是type为NodePort。这样,ingress就会暴露在集群节点ip的特定端口上。由于nodeport暴露的端口是随机端口,一般会在前面再搭建一套负载均衡器来转发请求。该方式一般用于宿主机是相对固定的环境ip地址不变的场景。NodePort方式暴露ingress虽然简单方便,但是NodePort多了一层NAT,在请求量级很大时可能对性能会有一定影响。
2.3//采用方式二:DaemonSet+HostNetwork+nodeSelector
(1)指定 nginx-ingress-controller 运行在 node02 节点
kubectl label node node02 ingress=truekubectl get nodes --show-labels
(2)修改 Deployment 为 DaemonSet ,指定节点运行,并开启 hostNetwork 网络
vim mandatory.yaml...apiVersion: apps/v1# 修改 kind# kind: Deploymentkind: DaemonSetmetadata: name: nginx-ingress-controller namespace: ingress-nginx labels: app.kubernetes.io/name: ingress-nginx app.kubernetes.io/part-of: ingress-nginxspec:# 删除Replicas# replicas: 1 selector: matchLabels: app.kubernetes.io/name: ingress-nginx app.kubernetes.io/part-of: ingress-nginx template: metadata: labels: app.kubernetes.io/name: ingress-nginx app.kubernetes.io/part-of: ingress-nginx annotations: prometheus.io/port: "10254" prometheus.io/scrape: "true" spec: # 使用主机网络 hostNetwork: true # 选择节点运行 nodeSelector: ingress: "true" serviceAccountName: nginx-ingress-serviceaccount......
(3)在所有 node 节点上传 nginx-ingress-controller 镜像压缩包 ingree.contro.tar.gz 到 /opt/ingress 目录,并解压和加载镜像
cd /opt/ingresstar zxvf ingree.contro.tar.gzdocker load -i ingree.contro.tar
(4)启动 nginx-ingress-controller
//nginx-ingress-controller 已经运行 node02 节点kubectl get pod -n ingress-nginx -o wideNAME READY STATUS RESTARTS AGE IP NODE NOMINATED NODE READINESS GATESnginx-ingress-controller-99h72 1/1 Running 0 93s 192.168.80.15 node02kubectl get cm,daemonset -n ingress-nginx -o wideNAME DATA AGEconfigmap/ingress-controller-leader-nginx 0 100sconfigmap/nginx-configuration 0 102sconfigmap/tcp-services 0 102sconfigmap/udp-services 0 102sNAME DESIRED CURRENT READY UP-TO-DATE AVAILABLE NODE SELECTOR AGEnginx-ingress-controller 1 1 1 1 1 ingress=true 16m//到 node02 节点查看netstat -lntp | grep nginxtcp 0 0 0.0.0.0:80 0.0.0.0:* LISTEN 7131/nginx: master tcp 0 0 0.0.0.0:8181 0.0.0.0:* LISTEN 7131/nginx: master tcp 0 0 0.0.0.0:443 0.0.0.0:* LISTEN 7131/nginx: master tcp6 0 0 :::10254 :::* LISTEN 7098/nginx-ingress-
由于配置了 hostnetwork,nginx 已经在 node 主机本地监听 80/443/8181 端口。其中 8181 是 nginx-controller 默认配置的一个 default backend(Ingress 资源没有匹配的 rule 对象时,流量就会被导向这个 default backend)。这样,只要访问 node 主机有公网 IP,就可以直接映射域名来对外网暴露服务了。如果要 nginx 高可用的话,可以在多个 node上部署,并在前面再搭建一套 LVS+keepalived 做负载均衡。
(5)创建 ingress 规则
//创建一个 deploy 和 svc
vim service-nginx.yamlapiVersion: apps/v1kind: Deploymentmetadata: name: nginx-appspec: replicas: 2 selector: matchLabels: app: nginx template: metadata: labels: app: nginx spec: containers: - name: nginx image: nginx imagePullPolicy: IfNotPresent ports: - containerPort: 80---apiVersion: v1kind: Servicemetadata: name: nginx-app-svcspec: type: ClusterIP ports: - protocol: TCP port: 80 targetPort: 80 selector: app: nginx
//创建 ingress
#方法一:(extensions/v1beta1 Ingress 在1.22版本即将弃用)vim ingress-app.yamlapiVersion: extensions/v1beta1kind: Ingressmetadata: name: nginx-app-ingressspec: rules: - host: www.kgc.com http: paths: - path: / backend: serviceName: nginx-app-svc servicePort: 80
#方法二:vim ingress-app.yaml apiVersion: networking.k8s.io/v1kind: Ingressmetadata: name: nginx-app-ingressspec: rules: - host: www.kgc.com http: paths: - path: / pathType: Prefix backend: service: name: nginx-app-svc port: number: 80
这里使用方法二:
kubectl apply -f service-nginx.yamlkubectl apply -f ingress-app.yamlkubectl get podsNAME READY STATUS RESTARTS AGEnginx-app-7bffc778db-sw2hl 1/1 Running 0 42snginx-app-7bffc778db-xsd5q 1/1 Running 0 42skubectl get ingressNAME HOSTS ADDRESS PORTS AGEnginx-app-ingress www.kgc.com 80 39s
(6)测试访问
//本地 host 添加域名解析vim /etc/hosts192.168.10.19 master192.168.10.20 node01192.168.10.21 node02192.168.10.21 www.kgc.comcurl www.kgc.com
(7)查看 nginx-ingress-controller
kubectl get pod -n ingress-nginx -o wideNAME READY STATUS RESTARTS AGE IP NODE NOMINATED NODE READINESS GATESnginx-ingress-controller-99h72 1/1 Running 0 93s 192.168.80.15 node02kubectl exec -it nginx-ingress-controller-99h72 -n ingress-nginx /bin/bash# more /etc/nginx/nginx.conf//可以看到从 start server www.kgc.com 到 end server www.kgc.com 之间包含了此域名用于反向代理的配置
2.4采用方式三:Deployment+NodePort模式的Service
(1)下载 nginx-ingress-controller 和 ingress-nginx 暴露端口配置文件
mkdir /opt/ingress-nodeportcd /opt/ingress-nodeport
官方下载地址:
wget https://raw.githubusercontent.com/kubernetes/ingress-nginx/nginx-0.30.0/deploy/static/mandatory.yamlwget https://raw.githubusercontent.com/kubernetes/ingress-nginx/nginx-0.30.0/deploy/static/provider/baremetal/service-nodeport.yaml
国内 gitee 资源地址:
wget https://gitee.com/mirrors/ingress-nginx/raw/nginx-0.30.0/deploy/static/mandatory.yamlwget https://gitee.com/mirrors/ingress-nginx/raw/nginx-0.30.0/deploy/static/provider/baremetal/service-nodeport.yaml
(2)在所有 node 节点上传镜像包 ingress-controller-0.30.0.tar 到 /opt/ingress-nodeport 目录,并加载镜像
docker load -i ingress-controller-0.30.0.tar
(3)启动 nginx-ingress-controller
kubectl apply -f mandatory.yamlkubectl apply -f service-nodeport.yaml
-------------------------------------------------------------------------------------------//如果K8S Pod 调度失败,在 kubectl describe pod资源时显示:Warning FailedScheduling 18s (x2 over 18s) default-scheduler 0/2 nodes are available: 2 node(s) didn"t match node selector
解决方案:1. 给需要调度的node加上对应标签# 相对上面这个Yaml文件的例子kubectl label nodes node_name kubernetes.io/os=linux
2. 删除Yaml文件中的nodeSelector,如果对节点没有要求的话,直接删除节点选择器即可-------------------------------------------------------------------------------------------
kubectl get pod,svc -n ingress-nginxNAME READY STATUS RESTARTS AGEpod/nginx-ingress-controller-7fcf8df75d-x47l8 1/1 Running 0 21mNAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGEservice/ingress-nginx NodePort 10.96.67.11980:32383/TCP,443:32133/TCP 2s
2.4.1Ingress HTTP 代理访问
cd /opt/ingress-nodeport
#创建 deployment、Service、Ingress Yaml 资源
vim ingress-nginx.yaml apiVersion: apps/v1kind: Deploymentmetadata: name: nginx-appspec: replicas: 2 selector: matchLabels: name: nginx template: metadata: labels: name: nginx spec: containers: - name: nginx image: nginx imagePullPolicy: IfNotPresent ports: - containerPort: 80---apiVersion: v1kind: Servicemetadata: name: nginx-svcspec: ports: - port: 80 targetPort: 80 protocol: TCP selector: name: nginx---apiVersion: networking.k8s.io/v1kind: Ingressmetadata: name: nginx-testspec: rules: - host: www.benet.com http: paths: - path: / pathType: Prefix backend: service: name: nginx-svc port: number: 80kubectl apply -f ingress-nginx.yaml
kubectl get svc,pods -o wideNAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE SELECTORservice/kubernetes ClusterIP 10.96.0.1443/TCP 8h service/nginx-svc ClusterIP 10.96.212.214 80/TCP 65s name=nginxNAME READY STATUS RESTARTS AGE IP NODE NOMINATED NODE READINESS GATESpod/nginx-app-65d7b99f6b-l4g65 1/1 Running 0 65s 10.244.1.8 node01 pod/nginx-app-65d7b99f6b-zcqgp 1/1 Running 0 65s 10.244.2.8 node02 kubectl exec -it pod/nginx-app-65d7b99f6b-l4g65 bash # cd /usr/share/nginx/html/ # echo "this is web1" >> index.html kubectl exec -it pod/nginx-app-65d7b99f6b-zcqgp bash # cd /usr/share/nginx/html/ # echo "this is web2" >> index.html
#测试访问curl 10.96.212.214kubectl get svc -n ingress-nginxNAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGEingress-nginx NodePort 10.96.67.11980:32383/TCP,443:32133/TCP 59m#本地 host 添加域名解析vim /etc/hosts192.168.80.10 master192.168.80.11 node01192.168.80.12 node02192.168.80.12 www.kgc.com www.benet.com#外部访问curl http://www.benet.com:32383
2.4.2Ingress HTTP 代理访问虚拟主机
mkdir /opt/ingress-nodeport/vhostcd /opt/ingress-nodeport/vhost
#创建虚拟主机1资源
vim deployment1.yamlapiVersion: apps/v1kind: Deploymentmetadata: name: deployment1spec: replicas: 2 selector: matchLabels: name: nginx1 template: metadata: labels: name: nginx1 spec: containers: - name: nginx1 image: soscscs/myapp:v1 imagePullPolicy: IfNotPresent ports: - containerPort: 80---apiVersion: v1kind: Servicemetadata: name: svc-1spec: ports: - port: 80 targetPort: 80 protocol: TCP selector: name: nginx1 kubectl apply -f deployment1.yaml
#创建虚拟主机2资源
vim deployment2.yamlapiVersion: apps/v1kind: Deploymentmetadata: name: deployment2spec: replicas: 2 selector: matchLabels: name: nginx2 template: metadata: labels: name: nginx2 spec: containers: - name: nginx2 image: soscscs/myapp:v2 imagePullPolicy: IfNotPresent ports: - containerPort: 80---apiVersion: v1kind: Servicemetadata: name: svc-2spec: ports: - port: 80 targetPort: 80 protocol: TCP selector: name: nginx2 kubectl apply -f deployment2.yaml
#创建ingress资源
vim ingress-nginx.yamlapiVersion: networking.k8s.io/v1kind: Ingressmetadata: name: ingress1spec: rules: - host: www1.kgc.com http: paths: - path: / pathType: Prefix backend: service: name: svc-1 port: number: 80---apiVersion: networking.k8s.io/v1kind: Ingressmetadata: name: ingress2spec: rules: - host: www2.kgc.com http: paths: - path: / pathType: Prefix backend: service: name: svc-2 port: number: 80kubectl apply -f ingress-nginx.yaml
#测试访问
kubectl get svc -n ingress-nginxNAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGEingress-nginx NodePort 10.96.67.11980:32383/TCP,443:32133/TCP 176mcurl www1.kgc.com:32383Hello MyApp | Version: v1 | Pod Namecurl www2.kgc.com:32383Hello MyApp | Version: v2 | Pod Name
2.4.3Ingress HTTPS 代理访问
mkdir /opt/ingress-nodeport/httpscd /opt/ingress-nodeport/https
#创建ssl证书
openssl req -x509 -sha256 -nodes -days 365 -newkey rsa:2048 -keyout tls.key -out tls.crt -subj "/CN=nginxsvc/O=nginxsvc"
#创建 secret 资源进行存储
kubectl create secret tls tls-secret --key tls.key --cert tls.crt
kubectl get secretNAME TYPE DATA AGEtls-secret kubernetes.io/tls 2 2m22skubectl describe secret tls-secretName: tls-secretNamespace: defaultLabels:Annotations: Type: kubernetes.io/tlsData====tls.crt: 1143 bytestls.key: 1704 bytes
#创建 deployment、Service、Ingress Yaml 资源
vim ingress-https.yamlapiVersion: apps/v1kind: Deploymentmetadata: name: nginx-appspec: replicas: 2 selector: matchLabels: name: nginx template: metadata: labels: name: nginx spec: containers: - name: nginx image: nginx imagePullPolicy: IfNotPresent ports: - containerPort: 80---apiVersion: v1kind: Servicemetadata: name: nginx-svcspec: ports: - port: 80 targetPort: 80 protocol: TCP selector: name: nginx---apiVersion: networking.k8s.io/v1kind: Ingressmetadata: name: nginx-httpsspec: tls: - hosts: - www3.kgc.com secretName: tls-secret rules: - host: www3.kgc.com http: paths: - path: / pathType: Prefix backend: service: name: nginx-svc port: number: 80kubectl apply -f ingress-https.yamlkubectl get svc -n ingress-nginxNAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGEingress-nginx NodePort 10.96.67.11980:32383/TCP,443:32133/TCP 3h41m
#访问测试在宿主机的 C:\Windows\System32\drivers\etc\hosts 文件中添加 192.168.10.10 www3.kgc.com 记录。使用谷歌浏览器访问 https://www3.kgc.com:31469
2.4.4Nginx 进行 BasicAuth
mkdir /opt/ingress-nodeport/basic-authcd /opt/ingress-nodeport/basic-auth
#生成用户密码认证文件,创建 secret 资源进行存储
yum -y install httpdhtpasswd -c auth zhangsan #认证文件名必须为 authkubectl create secret generic basic-auth --from-file=auth
#创建 ingress 资源
vim ingress-auth.yamlapiVersion: networking.k8s.io/v1kind: Ingressmetadata: name: ingress-auth annotations: #设置认证类型basic nginx.ingress.kubernetes.io/auth-type: basic #设置secret资源名称basic-auth nginx.ingress.kubernetes.io/auth-secret: basic-auth #设置认证窗口提示信息 nginx.ingress.kubernetes.io/auth-realm: "Authentication Required - zhangsan"spec: rules: - host: auth.kgc.com http: paths: - path: / pathType: Prefix backend: service: name: nginx-svc port: number: 80
//具体详细设置方法可参考官网https://kubernetes.github.io/ingress-nginx/examples/auth/basic/
kubectl apply -f ingress-auth.yaml
#访问测试kubectl get svc -n ingress-nginxNAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGEingress-nginx NodePort 10.96.67.11980:32383/TCP,443:32133/TCP 8hecho "192.168.10.10 auth.kgc.com" >> /etc/hosts浏览器访问:http://auth.kgc.com:32383
2.4.5Nginx 进行重写
#metadata.annotations 配置说明●nginx.ingress.kubernetes.io/rewrite-target: <字符串> #必须重定向流量的目标URI●nginx.ingress.kubernetes.io/ssl-redirect: <布尔值> #指示位置部分是否仅可访问SSL(当Ingress包含证书时,默认为true)●nginx.ingress.kubernetes.io/force-ssl-redirect: <布尔值> #即使Ingress未启用TLS,也强制重定向到HTTPS●nginx.ingress.kubernetes.io/app-root: <字符串> #定义Controller必须重定向的应用程序根,如果它在"/"上下文中●nginx.ingress.kubernetes.io/use-regex: <布尔值> #指示Ingress上定义的路径是否使用正则表达式
vim ingress-rewrite.yamlapiVersion: networking.k8s.io/v1kind: Ingressmetadata: name: nginx-rewrite annotations: nginx.ingress.kubernetes.io/rewrite-target: http://www1.kgc.com:32383spec: rules: - host: re.kgc.com http: paths: - path: / pathType: Prefix backend: #由于re.kgc.com只是用于跳转不需要真实站点存在,因此svc资源名称可随意定义 service: name: nginx-svc port: number: 80kubectl apply -f ingress-rewrite.yamlecho "192.168.80.10 re.kgc.com" >> /etc/hosts浏览器访问:http://re.kgc.com:32383
//总结ingress是k8s集群的请求入口,可以理解为对多个service的再次抽象通常说的ingress一般包括ingress资源对象及ingress-controller两部分组成ingress-controller有多种实现,社区原生的是ingress-nginx,根据具体需求选择ingress自身的暴露有多种方式,需要根据基础环境及业务类型选择合适的方式
关键词:
-

-

-

-
当前通讯!Python定制对象的独有特征
一、引入classOldboyStudent:school=& 39;oldboy& 39;defchoose_course(self):print(& 39;ischoosing
来源: 精准管控|AIRIOT数字油库智能化解决方案
今日热门!k8s对外服务之Ingress
开发中用到的配置文本文件
当前通讯!Python定制对象的独有特征
动态:3.8节大促:腾讯视频、QQ、绿钻、B站、百度网盘会员五折起
看点:钢琴弹出的声音怎么这么好听啊?离不开这四大件!
我国多地将体验超前温暖:郑州要破29℃ 但秋裤还不能脱
环球速看:当下最完美全面屏!京东方宣布独家供应努比亚Z50 Ultra
丧心病狂!这些人利用AI声音冒充亲人诈骗1100万美元
5步绘制高质量流程图
世界消息!朴素贝叶斯与Laplace平滑
一篇搞懂cookie和session
【环球速看料】生成你的自定义密码本Python
快看点丨8个月宝宝像打冷颤一样头抖_婴儿偶尔腿打颤正常吗
被批恶俗烂梗 鸡你太美商标无一注册成功:超20枚被判无效
即时看!AMD Yes!FSR 2.2插件已适用于虚幻引擎
环球焦点!V12自吸发动机+三电机!兰博基尼旗舰跑车动力信息公布:超千匹
天天即时看!招不到人!新加坡软件工程师月薪基本都超4.6万 跑不赢房租
微动态丨今晚打老虎!周杰伦用《赌侠2》梗回应周星驰喊话
当前快播:记一次影视cms黑盒CSRF->RCE
OpenYurt 在龙源 CNStack 云边协同项目的应用
当前资讯!注解:@RequiredArgsConstructor、 @Validated、 @Valid、 @Lazy
全球微动态丨MP 代码生成器工具类
焦点消息!2999元起!五菱羚羊智能电动自行车发布:新国标 200km续航
天猫超级红包开抢:今晚抢30万个6.8元天猫红包 最高3888元
观速讯丨育碧“壮士断腕”:将对欧洲工作室实施战略重组
天天热资讯!人民网评论:别让恶俗网络烂梗毒害孩子 散发恶臭气息
观速讯丨Win11强制要求的金身告破 TPM 2.0漏洞影响数十亿设备
天天头条:60% 程序员大呼:我要远程办公!
世界热消息:一篇文章带你了解折线图
焦点短讯!创建型-单例模式
世界要闻:18位身份证校验Python
【世界热闻】百度统计快速实现网站访问量的统计
环球速递!任长霞电视剧剧情
世界要闻:「全国两会跨省联动报道」一生·一世·一群鸟——黑颈鹤与贵州保护者刘广惠的故事
16+512GB杀到2799元 一加Ace 2V颠覆友商:便宜1000多
观热点:摄影小白也能瞬间变大师!努比亚Z50 Ultra视频评测:最完美的无孔全面屏
当前快报:杭州亚运倒计时200天!首批亚运电竞特许商品上线:史上首次
当前报道:首发749元 一加Buds Pro 2轻享版发布:丹拿联合调音
即时焦点:蔚来丹麦首座换电站上线:老外“跪”在地上观看
Linux常用的20个命令(上)
天天速递!全景剖析阿里云容器网络数据链路(六):ASM Istio
全球聚焦:gitee突然无法访问
【天天时快讯】自从用了 Stream,代码更简洁优雅了!
每日观察!拍了10多年星星!努比亚Z50 Ultra升级11大星空算法
今日看点:AI免费设计LOGO效果惊艳 雷军200万花早了
1.6L自吸最大功率99kW 2023款日产轩逸本月上市
焦点日报:一加Ace 2V首发主动增强式超级Wi-Fi:穿墙能力提升30%
全球快报:一加Ace 2V触控体验碾压iPhone 14 Pro Max:在安卓阵营中表现最佳
全球微动态丨为什么99%的程序员都做不好SQL优化?
当前通讯!跟老杜从零入门MyBatis到架构思维(一)MyBatis概述
告别数据开发中的人工审核!火山引擎 DataLeap 落地“自动校验开发规范”能力
每日播报!Markdown语法学习
赞美翡翠的优美句子有哪些?
【世界速看料】“APP刺客”倒逼厂商升级大内存、大存储!8+128根本不够用了
天天微速讯:一人改代码搞崩推特 马斯克气疯:全部重写!
天天观察:出演《狂飙》爆红!雷军晒“大嫂”高叶人像照:小米13徕卡镜头
全球短讯!若依项目部署详解
最新:python奇葩反爬-你是故意的还是不小心的
全球观焦点:(数据库系统概论|王珊)第十章数据库恢复技术-第四、五、六、七节:数据库恢复技术和数据库镜像
全球百事通!以图搜图实现
每日播报!四步教会你如何画好流程图?
每日快播:华昌集团
全球聚焦:你几点睡?全国熬夜最狠城市揭晓:广东最牛 干这些行业的熬夜最多
金俊秀为什么叫细亚俊秀?金俊秀个人简介资料
已考上大学的简短四字祝福语有哪些?祝福前途似锦的古诗词有哪些?
强迫性动作属抑郁症吗?强迫性动作的自我疗法有哪些?
天天热点评!嫌弃之余,百度的这些搜索技巧真得会!
环球热议:EF7数据库提供者的自定义值生成器
全球热议:Use CMake notes
ArrayList和LinkedList的区别
咬甲癖是心理疾病吗?咬甲癖怎么治疗?
皮肤剥离强迫症是什么?皮肤剥离强迫症怎么治疗?
中移动董事长喊话中小学必学编程:还有委员喊话取消英语主科学了没用 你支持谁?
【世界快播报】最受欢迎的豪华中大型SUV 新款宝马X5实车亮相:国产必卖爆
湖北省“最强9万元补贴”蔓延 云南东风本田抄作业:直补6万
热点在线丨比Dev渠道更“快”!微软为Windows新增Canary测试渠道
全球观热点:砸130亿元 日本又失败!新主力火箭发射后自毁 日本专家谈落后中国多少年
焦点!【ES三周年】Elasticsearch安全配置详解
时讯:【MRTK】修改 HoloLens 应用的默认系统设置
新动态:开心档之Python3 面向对象
面试官要你介绍项目,怎么说?
每日速读!git的使用(一篇非常好的文章)
【快播报】老杜带你从零入门MyBatis,学MyBatis看这篇就够了!
bt种子是什么意思?bt种子怎么变成文件?
怎么查询手机号的号主姓名?怎么查询手机号用了多少年?
cpu怎么看性能参数?cpu检测软件哪个好?
车主称极氪001空调喷白粉末 官方回应:符合国标没有损害
世界今热点:育碧参与 巴黎圣母院加速修复:力争明年重新开放
世界速看:为什么小米手机不在美国卖?看完原因对雷军更有好感
天天快看:魅族20 Pro真机照出炉:“纽扣”四摄有意思
今日聚焦!《卧龙》超猛玩家穿着内裤打Boss 张梁吕布都无奈了
传真机是干什么用的?怎么发传真?
吉吉影音是什么?吉吉影音手机版离线缓存怎么用?
【世界播资讯】封装发送短信功能的封装过程
快报:什么是流程图?一篇文章就帮你搞定了
建立私人知识网站 cpolar轻松做到1 (部署DokuWiki)
热点!cad块属性定义及应用
叶辰是什么电视剧
环球观速讯丨迷惑行为!女司机给奥迪Q3加玻璃水:一股脑全倒进机油壶